 |
API参考
|
 |
API参考
|
Public key infrastructure module. 更多...
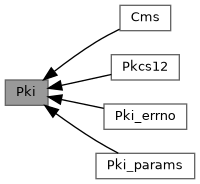
专题 | |
| Cms | |
| CMS processing interfaces. | |
| Pki_errno | |
| PKI-related error code definitions. | |
| Pki_params | |
| Parameter identifiers for PKI interfaces. | |
| Pkcs12 | |
| PKCS#12 processing interfaces. | |
类型定义 | |
| typedef int32_t(* | X509_STORECTX_VerifyCb) (int32_t, HITLS_X509_StoreCtx *) |
| Certificate chain build function. | |
函数 | |
| HITLS_X509_Cert * | HITLS_X509_CertNew (void) |
| Allocate a certificate. | |
| HITLS_X509_Cert * | HITLS_X509_ProviderCertNew (HITLS_PKI_LibCtx *libCtx, const char *attrName) |
| Create a new X509 certificate object using the provider mechanism | |
| void | HITLS_X509_CertFree (HITLS_X509_Cert *cert) |
| Unallocate a certificate. | |
| HITLS_X509_Cert * | HITLS_X509_CertDup (HITLS_X509_Cert *src) |
| Duplicate a certificate. | |
| int32_t | HITLS_X509_CertSign (int32_t mdId, const CRYPT_EAL_PkeyCtx *prvKey, const HITLS_X509_SignAlgParam *algParam, HITLS_X509_Cert *cert) |
| Sign a certificate. | |
| int32_t | HITLS_X509_CertDigest (HITLS_X509_Cert *cert, CRYPT_MD_AlgId mdId, uint8_t *data, uint32_t *dataLen) |
| Compute the digest of the certificate. | |
| int32_t | HITLS_X509_CertCtrl (HITLS_X509_Cert *cert, int32_t cmd, void *val, uint32_t valLen) |
| Generic function to process certificate. | |
| int32_t | HITLS_X509_CertParseBuff (int32_t format, const BSL_Buffer *encode, HITLS_X509_Cert **cert) |
| Parse the CERT in the buffer. | |
| int32_t | HITLS_X509_ProviderCertParseBuff (HITLS_PKI_LibCtx *libCtx, const char *attrName, const char *format, const BSL_Buffer *encode, HITLS_X509_Cert **cert) |
| Parse a certificate buffer using the provider mechanism | |
| int32_t | HITLS_X509_CertParseBundleBuff (int32_t format, const BSL_Buffer *encode, HITLS_X509_List **certlist) |
| Parse multiple certificates from a buffer. | |
| int32_t | HITLS_X509_ProviderCertParseBundleBuff (HITLS_PKI_LibCtx *libCtx, const char *attrName, const char *format, const BSL_Buffer *encode, HITLS_X509_List **certlist) |
| Parse multiple certificates from a buffer using the provider mechanism | |
| int32_t | HITLS_X509_CertParseFile (int32_t format, const char *path, HITLS_X509_Cert **cert) |
| Parse the CERT in the file. | |
| int32_t | HITLS_X509_ProviderCertParseFile (HITLS_PKI_LibCtx *libCtx, const char *attrName, const char *format, const char *path, HITLS_X509_Cert **cert) |
| Parse a certificate file using the provider mechanism | |
| int32_t | HITLS_X509_CertParseBundleFile (int32_t format, const char *path, HITLS_X509_List **certlist) |
| Parse the CERTs in the file. | |
| int32_t | HITLS_X509_ProviderCertParseBundleFile (HITLS_PKI_LibCtx *libCtx, const char *attrName, const char *format, const char *path, HITLS_X509_List **certlist) |
| Parse multiple certificates from a bundle file using the provider mechanism | |
| int32_t | HITLS_X509_CertGenBuff (int32_t format, HITLS_X509_Cert *cert, BSL_Buffer *buff) |
| Generates an encoded certificate. | |
| int32_t | HITLS_X509_CertGenFile (int32_t format, HITLS_X509_Cert *cert, const char *path) |
| Generate a certificate file. | |
| HITLS_X509_Crl * | HITLS_X509_CrlNew (void) |
| Allocate a crl. | |
| void | HITLS_X509_CrlFree (HITLS_X509_Crl *crl) |
| Release the CRL. | |
| int32_t | HITLS_X509_CrlCtrl (HITLS_X509_Crl *crl, int32_t cmd, void *val, uint32_t valLen) |
| Crl setting interface. | |
| int32_t | HITLS_X509_CrlParseBuff (int32_t format, const BSL_Buffer *encode, HITLS_X509_Crl **crl) |
| Parse the CRL in the buffer. | |
| int32_t | HITLS_X509_CrlParseBundleBuff (int32_t format, const BSL_Buffer *encode, HITLS_X509_List **crlList) |
| Parse multiple CRLs from a buffer. | |
| int32_t | HITLS_X509_CrlParseFile (int32_t format, const char *path, HITLS_X509_Crl **crl) |
| Parse the CRL in the file. | |
| int32_t | HITLS_X509_CrlParseBundleFile (int32_t format, const char *path, HITLS_X509_List **crlList) |
| Parse the CRLs in the file. | |
| int32_t | HITLS_X509_CrlGenBuff (int32_t format, HITLS_X509_Crl *crl, BSL_Buffer *buff) |
| Generate a CRL and encode it. | |
| int32_t | HITLS_X509_CrlGenFile (int32_t format, HITLS_X509_Crl *crl, const char *path) |
| Generate a CRL and encode it to specific file. | |
| int32_t | HITLS_X509_CrlVerify (void *pubkey, const HITLS_X509_Crl *crl) |
| Verify the integrity of the CRL. | |
| int32_t | HITLS_X509_CrlSign (int32_t mdId, const CRYPT_EAL_PkeyCtx *prvKey, const HITLS_X509_SignAlgParam *algParam, HITLS_X509_Crl *crl) |
| Signing a CRL. | |
| HITLS_X509_CrlEntry * | HITLS_X509_CrlEntryNew (void) |
| Allocate a revoked certificate. | |
| void | HITLS_X509_CrlEntryFree (HITLS_X509_CrlEntry *entry) |
| Release the CRL certificateRevoke struct . | |
| int32_t | HITLS_X509_CrlEntryCtrl (HITLS_X509_CrlEntry *revoked, int32_t cmd, void *val, uint32_t valLen) |
| Control interface for CRL entry. | |
| HITLS_X509_Csr * | HITLS_X509_CsrNew (void) |
| Allocate a pkcs10 csr. | |
| HITLS_X509_Csr * | HITLS_X509_ProviderCsrNew (HITLS_PKI_LibCtx *libCtx, const char *attrName) |
| Create a new csr object using the provider mechanism | |
| void | HITLS_X509_CsrFree (HITLS_X509_Csr *csr) |
| Release the pkcs10 csr. | |
| int32_t | HITLS_X509_CsrSign (int32_t mdId, const CRYPT_EAL_PkeyCtx *prvKey, const HITLS_X509_SignAlgParam *algParam, HITLS_X509_Csr *csr) |
| Sign a CSR (Certificate Signing Request). | |
| int32_t | HITLS_X509_CsrGenBuff (int32_t format, HITLS_X509_Csr *csr, BSL_Buffer *buff) |
| Generate csr to store in buffer | |
| int32_t | HITLS_X509_CsrGenFile (int32_t format, HITLS_X509_Csr *csr, const char *path) |
| Generate csr to store in file | |
| int32_t | HITLS_X509_CsrCtrl (HITLS_X509_Csr *csr, int32_t cmd, void *val, uint32_t valLen) |
| Generic function to process csr function | |
| int32_t | HITLS_X509_CsrParseBuff (int32_t format, const BSL_Buffer *encode, HITLS_X509_Csr **csr) |
| Parse the csr in the buffer.When the parameter is BSL_FORMAT_PEM and BSL_FORMAT_UNKNOWN, the buff of encode needs to end with '\0' | |
| int32_t | HITLS_X509_CsrParseFile (int32_t format, const char *path, HITLS_X509_Csr **csr) |
| Parse the csr in the file | |
| int32_t | HITLS_X509_CsrVerify (HITLS_X509_Csr *csr) |
| Csr verify function | |
| int32_t | HITLS_X509_ExtCtrl (HITLS_X509_Ext *ext, int32_t cmd, void *val, uint32_t valLen) |
| Generic function to set/get an extension. | |
| HITLS_X509_Ext * | HITLS_X509_ExtNew (int32_t type) |
| Allocate a extension. | |
| void | HITLS_X509_ExtFree (HITLS_X509_Ext *ext) |
| Unallocate a extension. | |
| void | HITLS_X509_ClearAuthorityKeyId (HITLS_X509_ExtAki *aki) |
| clear the HITLS_X509_ExtAki structure. | |
| void | HITLS_X509_FreeGeneralName (HITLS_X509_GeneralName *data) |
| Free a general name. | |
| BslList * | HITLS_X509_DnListNew (void) |
| New a list of distinguish name, the item is HITLS_X509_NameNode. | |
| void | HITLS_X509_DnListFree (BslList *dnList) |
| New a list of distinguish name, the list . | |
| int32_t | HITLS_X509_AddDnName (BslList *list, HITLS_X509_DN *dnNames, uint32_t size) |
| Add a distinguish name array to list. | |
| int32_t | HITLS_X509_AttrCtrl (HITLS_X509_Attrs *attributes, HITLS_X509_AttrCmd cmd, void *val, uint32_t valLen) |
| Generic function to process attribute function | |
| HITLS_X509_StoreCtx * | HITLS_X509_StoreCtxNew (void) |
| Allocate a StoreCtx. | |
| HITLS_X509_StoreCtx * | HITLS_X509_ProviderStoreCtxNew (HITLS_PKI_LibCtx *libCtx, const char *attrName) |
| Create a new X509 store object using the provider mechanism | |
| void | HITLS_X509_StoreCtxFree (HITLS_X509_StoreCtx *storeCtx) |
| Release the StoreCtx. | |
| int32_t | HITLS_X509_StoreCtxCtrl (HITLS_X509_StoreCtx *storeCtx, int32_t cmd, void *val, uint32_t valLen) |
| Generic function to process StoreCtx. | |
| int32_t | HITLS_X509_CertVerify (HITLS_X509_StoreCtx *storeCtx, HITLS_X509_List *chain) |
| Certificate chain verify function. | |
| int32_t | HITLS_X509_CertVerifyByPubKey (HITLS_X509_Cert *cert, CRYPT_EAL_PkeyCtx *pubKey) |
| Verify a single certificate's signature using an external public key. | |
| int32_t | HITLS_X509_CertChainBuild (HITLS_X509_StoreCtx *storeCtx, bool isWithRoot, HITLS_X509_Cert *cert, HITLS_X509_List **chain) |
| Certificate chain build function. | |
| int32_t | HITLS_X509_VerifyHostname (HITLS_X509_Cert *cert, uint32_t flags, const char *hostname, uint32_t hostnameLen) |
| Verifies a certificate's hostname according to RFC6125 and RFC9525. It first checks for a matching dNSName in the Subject Alternative Name (SAN) extension. If, and only if, no dNSName entries are present, it falls back to check the Common Name (CN). flags: | |
| int32_t | HITLS_X509_CheckKey (HITLS_X509_Cert *cert, CRYPT_EAL_PkeyCtx *prvKey) |
| Verify that a certificate's public key matches a given private key. | |
Public key infrastructure module.
| typedef int32_t(* X509_STORECTX_VerifyCb) (int32_t, HITLS_X509_StoreCtx *) |
Certificate chain build function.
| int32_t | [IN] Current error code for the current error. |
| HITLS_X509_StoreCtx | [IN] X509store handle. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_AddDnName | ( | BslList * | list, |
| HITLS_X509_DN * | dnNames, | ||
| uint32_t | size ) |
Add a distinguish name array to list.
| list | [IN] The name list |
| dnNames | [IN] dnName array |
| size | [IN] The count of dnName array |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_AttrCtrl | ( | HITLS_X509_Attrs * | attributes, |
| HITLS_X509_AttrCmd | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Generic function to process attribute function
| attributes | [IN] The attribute list |
| cmd | [IN] HITLS_X509_AttrCmd |
| val | data type HITLS_X509_ATTR_XX_REQUESTED_EXTENSIONS HITLS_X509_Ext |
| valLen | The length of value. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertChainBuild | ( | HITLS_X509_StoreCtx * | storeCtx, |
| bool | isWithRoot, | ||
| HITLS_X509_Cert * | cert, | ||
| HITLS_X509_List ** | chain ) |
Certificate chain build function.
| storeCtx | [IN] StoreCtx. |
| isWithRoot | [IN] whether the root cert is included and from trusted store. It is not affected by the partial certificate chain verification flag. |
| cert | [IN] certificate. |
| chain | [OUT] certificate chain. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertCtrl | ( | HITLS_X509_Cert * | cert, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Generic function to process certificate.
| cert | [IN] The certificate. |
| cmd | [IN] HITLS_X509_Cmd |
| val | [IN/OUT] input and output value |
| valLen | [In] value length |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertDigest | ( | HITLS_X509_Cert * | cert, |
| CRYPT_MD_AlgId | mdId, | ||
| uint8_t * | data, | ||
| uint32_t * | dataLen ) |
Compute the digest of the certificate.
| cert | [IN] The certificate. |
| mdId | [IN] Digest algorithm. |
| data | [IN/OUT] The digest result. |
| dataLen | [IN/OUT] The length of the digest. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| HITLS_X509_Cert * HITLS_X509_CertDup | ( | HITLS_X509_Cert * | src | ) |
Duplicate a certificate.
| src | [IN] Source certificate. |
| HITLS_X509_Cert | *, success. NULL, fail. |
| void HITLS_X509_CertFree | ( | HITLS_X509_Cert * | cert | ) |
Unallocate a certificate.
| cert | [IN] The certificate. |
| int32_t HITLS_X509_CertGenBuff | ( | int32_t | format, |
| HITLS_X509_Cert * | cert, | ||
| BSL_Buffer * | buff ) |
Generates an encoded certificate.
| format | [IN] Encoding format: BSL_FORMAT_ASN1 or BSL_FORMAT_PEM |
| cert | [IN] cert |
| buff | [OUT] encode result |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertGenFile | ( | int32_t | format, |
| HITLS_X509_Cert * | cert, | ||
| const char * | path ) |
Generate a certificate file.
| format | [IN] Encoding format: BSL_FORMAT_ASN1 or BSL_FORMAT_PEM |
| cert | [IN] cert |
| path | [IN] file path |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| HITLS_X509_Cert * HITLS_X509_CertNew | ( | void | ) |
Allocate a certificate.
| HITLS_X509_Cert | * |
| int32_t HITLS_X509_CertParseBuff | ( | int32_t | format, |
| const BSL_Buffer * | encode, | ||
| HITLS_X509_Cert ** | cert ) |
Parse the CERT in the buffer.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| encode | [IN] CERT data. BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| cert | [OUT] CERT after parse. |
| int32_t HITLS_X509_CertParseBundleBuff | ( | int32_t | format, |
| const BSL_Buffer * | encode, | ||
| HITLS_X509_List ** | certlist ) |
Parse multiple certificates from a buffer.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| encode | [IN] Certificate data buffer. BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| certlist | [OUT] Certificate list after parsing. |
| int32_t HITLS_X509_CertParseBundleFile | ( | int32_t | format, |
| const char * | path, | ||
| HITLS_X509_List ** | certlist ) |
Parse the CERTs in the file.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| path | [IN] Certificate file path. |
| certlist | [OUT] Certificate list after parse. |
| int32_t HITLS_X509_CertParseFile | ( | int32_t | format, |
| const char * | path, | ||
| HITLS_X509_Cert ** | cert ) |
Parse the CERT in the file.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| path | [IN] CERT file path. |
| cert | [OUT] CERT after parse. |
| int32_t HITLS_X509_CertSign | ( | int32_t | mdId, |
| const CRYPT_EAL_PkeyCtx * | prvKey, | ||
| const HITLS_X509_SignAlgParam * | algParam, | ||
| HITLS_X509_Cert * | cert ) |
Sign a certificate.
| mdId | [IN] The message digest algorithm ID. |
| prvKey | [IN] The private key context used for signing. |
| algParam | [IN] The signature algorithm parameters. |
| cert | [IN] The certificate to be signed. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertVerify | ( | HITLS_X509_StoreCtx * | storeCtx, |
| HITLS_X509_List * | chain ) |
Certificate chain verify function.
| storeCtx | [IN] StoreCtx. |
| chain | [IN] certificate chain. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CertVerifyByPubKey | ( | HITLS_X509_Cert * | cert, |
| CRYPT_EAL_PkeyCtx * | pubKey ) |
Verify a single certificate's signature using an external public key.
| cert | [IN] Certificate to be verified. |
| pubKey | [IN] Public key context used to verify the certificate. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CheckKey | ( | HITLS_X509_Cert * | cert, |
| CRYPT_EAL_PkeyCtx * | prvKey ) |
Verify that a certificate's public key matches a given private key.
| cert | [IN] Certificate containing the public key to check |
| prvKey | [IN] Private key to verify against the certificate |
| #HITLS_PKI_SUCCESS | if the private key matches the certificate's public key. |
| #HITLS_X509_ERR_CERT_INVALID_PUBKEY | if the keys do not match or signing/verification fails. |
| Other | error codes can be found in hitls_pki_errno.h |
| void HITLS_X509_ClearAuthorityKeyId | ( | HITLS_X509_ExtAki * | aki | ) |
clear the HITLS_X509_ExtAki structure.
| aki | [IN] The HITLS_X509_ExtAki aki |
| int32_t HITLS_X509_CrlCtrl | ( | HITLS_X509_Crl * | crl, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Crl setting interface.
| crl | [IN] CRL data |
| cmd | [IN] Set type. |
| val | [OUT] Set data. |
| valLen | [IN] The length of val. |
| int32_t HITLS_X509_CrlEntryCtrl | ( | HITLS_X509_CrlEntry * | revoked, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Control interface for CRL entry.
| revoked | [IN] CRL entry to control. |
| cmd | [IN] Control command. |
| val | [IN/OUT] Control value. |
| valLen | [IN] Length of control value. |
| void HITLS_X509_CrlEntryFree | ( | HITLS_X509_CrlEntry * | entry | ) |
Release the CRL certificateRevoke struct .
| entry | [IN] entry info. |
| HITLS_X509_CrlEntry * HITLS_X509_CrlEntryNew | ( | void | ) |
Allocate a revoked certificate.
| void HITLS_X509_CrlFree | ( | HITLS_X509_Crl * | crl | ) |
Release the CRL.
| crl | [IN] CRL after parse. |
| int32_t HITLS_X509_CrlGenBuff | ( | int32_t | format, |
| HITLS_X509_Crl * | crl, | ||
| BSL_Buffer * | buff ) |
Generate a CRL and encode it.
| format | [IN] Encoding format: BSL_FORMAT_PEM or BSL_FORMAT_ASN1. |
| crl | [IN] CRL raw data. |
| buff | [OUT] Encode data. |
| int32_t HITLS_X509_CrlGenFile | ( | int32_t | format, |
| HITLS_X509_Crl * | crl, | ||
| const char * | path ) |
Generate a CRL and encode it to specific file.
| format | [IN] Encoding format: BSL_FORMAT_PEM or BSL_FORMAT_ASN1. |
| crl | [IN] CRL raw data. |
| path | [OUT] Encoding data file path. |
| HITLS_X509_Crl * HITLS_X509_CrlNew | ( | void | ) |
Allocate a crl.
| HITLS_X509_Crl | * |
| int32_t HITLS_X509_CrlParseBuff | ( | int32_t | format, |
| const BSL_Buffer * | encode, | ||
| HITLS_X509_Crl ** | crl ) |
Parse the CRL in the buffer.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| encode | [IN] CRL data. BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| crl | [OUT] CRL after parse. |
| int32_t HITLS_X509_CrlParseBundleBuff | ( | int32_t | format, |
| const BSL_Buffer * | encode, | ||
| HITLS_X509_List ** | crlList ) |
Parse multiple CRLs from a buffer.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| encode | [IN] CRL data buffer. BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| crlList | [OUT] List of parsed CRL objects. |
| int32_t HITLS_X509_CrlParseBundleFile | ( | int32_t | format, |
| const char * | path, | ||
| HITLS_X509_List ** | crlList ) |
Parse the CRLs in the file.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/ BSL_FORMAT_UNKNOWN. |
| path | [IN] CRL file path. |
| crllist | [OUT] CRL list after parse. |
| int32_t HITLS_X509_CrlParseFile | ( | int32_t | format, |
| const char * | path, | ||
| HITLS_X509_Crl ** | crl ) |
Parse the CRL in the file.
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN. |
| path | [IN] CRL file path. |
| crl | [OUT] CRL after parse. |
| int32_t HITLS_X509_CrlSign | ( | int32_t | mdId, |
| const CRYPT_EAL_PkeyCtx * | prvKey, | ||
| const HITLS_X509_SignAlgParam * | algParam, | ||
| HITLS_X509_Crl * | crl ) |
Signing a CRL.
| mdId | [IN] hash algorithm. |
| prvKey | [IN] private key. |
| algParam | [IN] signature parameter, for example, rsa-pss parameter. |
| crl | [IN/OUT] CRL info. |
| int32_t HITLS_X509_CrlVerify | ( | void * | pubkey, |
| const HITLS_X509_Crl * | crl ) |
Verify the integrity of the CRL.
| pubkey | [IN] pubkey. |
| crl | [IN] CRL info. |
| int32_t HITLS_X509_CsrCtrl | ( | HITLS_X509_Csr * | csr, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Generic function to process csr function
| csr | [IN] The csr context |
| cmd | [IN] HITLS_X509_Cmd |
| val | [IN/OUT] input and output value. |
| valLen | [IN] value length. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| void HITLS_X509_CsrFree | ( | HITLS_X509_Csr * | csr | ) |
Release the pkcs10 csr.
| csr | [IN] CSR context. |
| void |
| int32_t HITLS_X509_CsrGenBuff | ( | int32_t | format, |
| HITLS_X509_Csr * | csr, | ||
| BSL_Buffer * | buff ) |
Generate csr to store in buffer
| format | [IN] The format of the generated csr: BSL_FORMAT_ASN1/BSL_FORMAT_PEM |
| csr | [IN] The csr context |
| buff | [OUT] The buffer of the generated csr. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CsrGenFile | ( | int32_t | format, |
| HITLS_X509_Csr * | csr, | ||
| const char * | path ) |
Generate csr to store in file
| format | [IN] The format of the generated csr: BSL_FORMAT_ASN1/BSL_FORMAT_PEM |
| csr | [IN] The csr context |
| path | [IN] The path of the generated csr. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| HITLS_X509_Csr * HITLS_X509_CsrNew | ( | void | ) |
Allocate a pkcs10 csr.
| HITLS_X509_Csr | * |
| int32_t HITLS_X509_CsrParseBuff | ( | int32_t | format, |
| const BSL_Buffer * | encode, | ||
| HITLS_X509_Csr ** | csr ) |
Parse the csr in the buffer.When the parameter is BSL_FORMAT_PEM and BSL_FORMAT_UNKNOWN, the buff of encode needs to end with '\0'
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1 |
| encode | [IN] The csr data BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| csr | [OUT] The csr context after parsing |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CsrParseFile | ( | int32_t | format, |
| const char * | path, | ||
| HITLS_X509_Csr ** | csr ) |
Parse the csr in the file
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1 |
| path | [IN] The csr file path |
| csr | [OUT] The csr context after parsing |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CsrSign | ( | int32_t | mdId, |
| const CRYPT_EAL_PkeyCtx * | prvKey, | ||
| const HITLS_X509_SignAlgParam * | algParam, | ||
| HITLS_X509_Csr * | csr ) |
Sign a CSR (Certificate Signing Request).
| mdId | [IN] The message digest algorithm ID. |
| prvKey | [IN] The private key context used for signing. |
| algParam | [IN] The signature algorithm parameters. |
| csr | [IN] The CSR to be signed. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| int32_t HITLS_X509_CsrVerify | ( | HITLS_X509_Csr * | csr | ) |
Csr verify function
| csr | [IN] The csr context |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| void HITLS_X509_DnListFree | ( | BslList * | dnList | ) |
New a list of distinguish name, the list .
| list | [IN] The name list |
| void |
| BslList * HITLS_X509_DnListNew | ( | void | ) |
New a list of distinguish name, the item is HITLS_X509_NameNode.
| BslList | *, success. error return NULL. |
| int32_t HITLS_X509_ExtCtrl | ( | HITLS_X509_Ext * | ext, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Generic function to set/get an extension.
| ext | [IN] extensions |
| cmd | [IN] HITLS_X509_EXT_SET_XXX cmd data type HITLS_X509_EXT_GET|SET_KUSAGE HITLS_X509_ExtKeyUsage HITLS_X509_EXT_GET|SET_BCONS HITLS_X509_ExtBCons HITLS_X509_EXT_GET|SET_AKI HITLS_X509_ExtAki HITLS_X509_EXT_GET|SET_SKI HITLS_X509_ExtSki HITLS_X509_EXT_GET|SET_SAN HITLS_X509_ExtSan HITLS_X509_EXT_GET|SET_EXKUSAGE HITLS_X509_ExtExKeyUsage HITLS_X509_EXT_CHECK_SKI bool |
| val | [IN/OUT] input and output value |
| valLen | [In] value length |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| void HITLS_X509_ExtFree | ( | HITLS_X509_Ext * | ext | ) |
Unallocate a extension.
| ext | [IN] The extension. |
| HITLS_X509_Ext * HITLS_X509_ExtNew | ( | int32_t | type | ) |
Allocate a extension.
| HITLS_X509_Ext | * |
| void HITLS_X509_FreeGeneralName | ( | HITLS_X509_GeneralName * | data | ) |
Free a general name.
| data | [IN] The general name. |
| HITLS_X509_Cert * HITLS_X509_ProviderCertNew | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName ) |
Create a new X509 certificate object using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| int32_t HITLS_X509_ProviderCertParseBuff | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName, | ||
| const char * | format, | ||
| const BSL_Buffer * | encode, | ||
| HITLS_X509_Cert ** | cert ) |
Parse a certificate buffer using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| format | [IN] Encoding format: BSL_FORMAT_PEM/BSL_FORMAT_ASN1/BSL_FORMAT_UNKNOWN |
| encode | [IN] Certificate data buffer BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| cert | [OUT] Parsed certificate object |
| int32_t HITLS_X509_ProviderCertParseBundleBuff | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName, | ||
| const char * | format, | ||
| const BSL_Buffer * | encode, | ||
| HITLS_X509_List ** | certlist ) |
Parse multiple certificates from a buffer using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| format | [IN] Encoding format: "PEM"/"ASN1"/NULL |
| encode | [IN] Certificate data buffer BSL_FORMAT_UNKNOWN/BSL_FORMAT_PEM: the buff of encode needs to end with '\0' the dataLen should exclude the end '\0' |
| certlist | [OUT] List of parsed certificate objects |
| int32_t HITLS_X509_ProviderCertParseBundleFile | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName, | ||
| const char * | format, | ||
| const char * | path, | ||
| HITLS_X509_List ** | certlist ) |
Parse multiple certificates from a bundle file using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| format | [IN] Encoding format: "PEM"/"ASN1"/NULL |
| path | [IN] Certificate bundle file path |
| certlist | [OUT] List of parsed certificate objects |
| int32_t HITLS_X509_ProviderCertParseFile | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName, | ||
| const char * | format, | ||
| const char * | path, | ||
| HITLS_X509_Cert ** | cert ) |
Parse a certificate file using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| format | [IN] Encoding format: "PEM"/"ASN1"/NULL |
| path | [IN] Certificate file path |
| cert | [OUT] Parsed certificate object |
| HITLS_X509_Csr * HITLS_X509_ProviderCsrNew | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName ) |
Create a new csr object using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL_LibCtx |
| attrName | [IN] Provider attribute name for capability matching |
| HITLS_X509_StoreCtx * HITLS_X509_ProviderStoreCtxNew | ( | HITLS_PKI_LibCtx * | libCtx, |
| const char * | attrName ) |
Create a new X509 store object using the provider mechanism
| libCtx | [IN] Library context from CRYPT_EAL |
| attrName | [IN] Provider attribute name for capability matching |
| int32_t HITLS_X509_StoreCtxCtrl | ( | HITLS_X509_StoreCtx * | storeCtx, |
| int32_t | cmd, | ||
| void * | val, | ||
| uint32_t | valLen ) |
Generic function to process StoreCtx.
| storeCtx | [IN] StoreCtx. |
| cmd | [IN] HITLS_X509_StoreCtxCmd data type data length HITLS_X509_STORECTX_SET_PARAM_DEPTH int32_t sizeof(int32_t) HITLS_X509_STORECTX_SET_PARAM_FLAGS uint64_t sizeof(uint64_t) HITLS_X509_STORECTX_SET_PURPOSE uint64_t sizeof(uint64_t) HITLS_X509_STORECTX_SET_TIME int64_t sizeof(int64_t) HITLS_X509_STORECTX_SET_SECBITS uint32_t sizeof(uint32_t) HITLS_X509_STORECTX_CLR_PARAM_FLAGS uint64_t sizeof(uint64_t) HITLS_X509_STORECTX_DEEP_COPY_SET_CA HITLS_X509_Cert - HITLS_X509_STORECTX_SHALLOW_COPY_SET_CA HITLS_X509_Cert - HITLS_X509_STORECTX_SET_CRL HITLS_X509_Crl - HITLS_X509_STORECTX_SET_VFY_SM2_USERID buffer > 0 HITLS_X509_STORECTX_SET_VERIFY_CB callback function sizeof(callback function) HITLS_X509_STORECTX_SET_USR_DATA void * sizeof(void *) HITLS_X509_STORECTX_ADD_CA_PATH char * string length HITLS_X509_STORECTX_CLEAR_CRL NULL 0 HITLS_X509_STORECTX_REF_UP int sizeof(int) HITLS_X509_STORECTX_GET_PARAM_DEPTH int32_t * sizeof(int32_t) HITLS_X509_STORECTX_GET_VERIFY_CB callback function * sizeof(callback function) HITLS_X509_STORECTX_GET_USR_DATA void ** sizeof(void *) HITLS_X509_STORECTX_GET_PARAM_FLAGS uint64_t * sizeof(uint64_t) HITLS_X509_STORECTX_SET_ERROR int32_t sizeof(int32_t) HITLS_X509_STORECTX_GET_ERROR int32_t * sizeof(int32_t) HITLS_X509_STORECTX_GET_CUR_CERT HITLS_X509_Cert ** sizeof(HITLS_X509_Cert *) HITLS_X509_STORECTX_SET_CUR_DEPTH int32_t sizeof(int32_t) HITLS_X509_STORECTX_GET_CUR_DEPTH int32_t * sizeof(int32_t) HITLS_X509_STORECTX_GET_CERT_CHAIN HITLS_X509_List ** sizeof(HITLS_X509_List *) |
| val | [IN/OUT] input and output value. |
| valLen | [IN] value length. |
| #HITLS_PKI_SUCCESS,success. | Error codes can be found in hitls_pki_errno.h |
| void HITLS_X509_StoreCtxFree | ( | HITLS_X509_StoreCtx * | storeCtx | ) |
Release the StoreCtx.
| storeCtx | [IN] StoreCtx. |
| void |
| HITLS_X509_StoreCtx * HITLS_X509_StoreCtxNew | ( | void | ) |
Allocate a StoreCtx.
| HITLS_X509_StoreCtx | * |
| int32_t HITLS_X509_VerifyHostname | ( | HITLS_X509_Cert * | cert, |
| uint32_t | flags, | ||
| const char * | hostname, | ||
| uint32_t | hostnameLen ) |
Verifies a certificate's hostname according to RFC6125 and RFC9525. It first checks for a matching dNSName in the Subject Alternative Name (SAN) extension. If, and only if, no dNSName entries are present, it falls back to check the Common Name (CN). flags:
| cert | [IN] The certificate to verify. |
| flags | [IN] A flag controlling wildcard matching behavior. |
| hostname | [IN] The hostname to match against. |
| hostnameLen | [IN] The length of the hostname. |
| #HITLS_PKI_SUCCESS | if the hostname is successfully verified. |
| #HITLS_X509_ERR_VFY_HOSTNAME_FAIL | if the hostname does not match. |
| Other | error codes for parsing or parameter errors. |