 |
API参考
|
 |
API参考
|
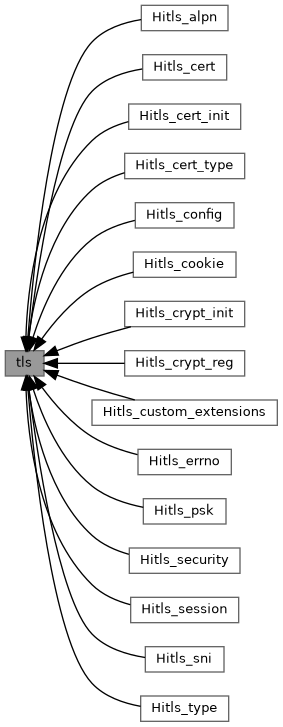
专题 | |
| Hitls_alpn | |
| TLS ALPN related type | |
| Hitls_cert | |
| TLS Certificate Operation Interface | |
| Hitls_cert_init | |
| TLS certificate abstraction layer initialization | |
| Hitls_cert_type | |
| Structures related to a certificate | |
| Hitls_config | |
| TLS parameter configuration | |
| Hitls_cookie | |
| DTLS cookie generation and verification callbacks. | |
| Hitls_crypt_init | |
| algorithm abstraction layer initialization | |
| Hitls_crypt_reg | |
| Algorithm related interfaces to be registered | |
| Hitls_custom_extensions | |
| TLS Custom Extensions | |
| Hitls_errno | |
| error module | |
| Hitls_psk | |
| Basic functions for link establishment based on PSK | |
| Hitls_security | |
| TLS security features | |
| Hitls_session | |
| TLS session | |
| Hitls_sni | |
| TLS SNI correlation type | |
| Hitls_type | |
| TLS type definition, provides the TLS type required by the user | |
函数 | |
| HITLS_Ctx * | HITLS_New (HITLS_Config *config) |
| Create a TLS object and deep copy the HITLS_Config to the HITLS_Ctx. | |
| void | HITLS_Free (HITLS_Ctx *ctx) |
| Release the TLS connection. | |
| int32_t | HITLS_Clear (HITLS_Ctx *ctx) |
| Reset the TLS handle to allow it to be used for another connection. | |
| int32_t | HITLS_SetUio (HITLS_Ctx *ctx, BSL_UIO *uio) |
| Set the UIO object for the HiTLS context. | |
| int32_t | HITLS_SetReadUio (HITLS_Ctx *ctx, BSL_UIO *uio) |
| Read UIO for the HiTLS context. | |
| BSL_UIO * | HITLS_GetUio (const HITLS_Ctx *ctx) |
| Obtain the UIO object from the HiTLS context. | |
| BSL_UIO * | HITLS_GetReadUio (const HITLS_Ctx *ctx) |
| Obtain the UIO object of the read data. | |
| int32_t | HITLS_Connect (HITLS_Ctx *ctx) |
| The client starts the handshake with the TLS server. | |
| int32_t | HITLS_SetEndPoint (HITLS_Ctx *ctx, bool isClient) |
| Set the initial status of the connection. | |
| int32_t | HITLS_Accept (HITLS_Ctx *ctx) |
| The server waits for the client to start handshake. | |
| int32_t | HITLS_Listen (HITLS_Ctx *ctx, BSL_SAL_SockAddr clientAddr) |
| The server statelessly listens for new incoming DTLS connections. | |
| int32_t | HITLS_Read (HITLS_Ctx *ctx, uint8_t *data, uint32_t bufSize, uint32_t *readLen) |
| Read application data | |
| int32_t | HITLS_Peek (HITLS_Ctx *ctx, uint8_t *data, uint32_t bufSize, uint32_t *readLen) |
| read application data from a TLS/SSL connection | |
| int32_t | HITLS_Write (HITLS_Ctx *ctx, const uint8_t *data, uint32_t dataLen, uint32_t *writeLen) |
| Write data. | |
| int32_t | HITLS_GetMaxWriteSize (const HITLS_Ctx *ctx, uint32_t *len) |
| Obtain the maximum writable (plaintext) length. | |
| void * | HITLS_GetUserData (const HITLS_Ctx *ctx) |
| Obtain user data from the HiTLS context. This interface is called in the callback registered with the HiTLS. | |
| int32_t | HITLS_SetUserData (HITLS_Ctx *ctx, void *userData) |
| Save the user data in the HiTLS context, which can be obtained from the callback registered with the HiTLS. | |
| int32_t | HITLS_Close (HITLS_Ctx *ctx) |
| Close the TLS connection. | |
| int32_t | HITLS_SetShutdownState (HITLS_Ctx *ctx, uint32_t mode) |
| Set the shutdown status of the TLS link. | |
| int32_t | HITLS_GetShutdownState (const HITLS_Ctx *ctx, uint32_t *mode) |
| Obtain the shutdown status of the TLS link. | |
| int32_t | HITLS_GetNegotiatedVersion (const HITLS_Ctx *ctx, uint16_t *version) |
| Obtain the HiTLS negotiation version. | |
| int32_t | HITLS_GetMaxProtoVersion (const HITLS_Ctx *ctx, uint16_t *maxVersion) |
| Obtain the latest protocol version. | |
| int32_t | HITLS_GetMinProtoVersion (const HITLS_Ctx *ctx, uint16_t *minVersion) |
| Obtain the latest protocol version. | |
| int32_t | HITLS_SetMinProtoVersion (HITLS_Ctx *ctx, uint16_t version) |
| Set the minimum protocol version based on the specified version. | |
| int32_t | HITLS_SetMaxProtoVersion (HITLS_Ctx *ctx, uint16_t version) |
| Set the maximum protocol version that is supported based on the specified version. | |
| int32_t | HITLS_IsAead (const HITLS_Ctx *ctx, bool *isAead) |
| Obtain whether to use the AEAD algorithm. | |
| int32_t | HITLS_IsDtls (const HITLS_Ctx *ctx, bool *isDtls) |
| Check whether DTLS is used. | |
| int32_t | HITLS_SetErrorCode (HITLS_Ctx *ctx, int32_t errorCode) |
| Record the error value of the HiTLS link. | |
| int32_t | HITLS_GetErrorCode (const HITLS_Ctx *ctx) |
| Obtain the error value of the HiTLS link. | |
| int32_t | HITLS_IsHandShakeDone (const HITLS_Ctx *ctx, uint8_t *isDone) |
| Obtain the information about whether the handshake is complete. | |
| int32_t | HITLS_IsServer (const HITLS_Ctx *ctx, bool *isServer) |
| Indicates whether the HiTLS object functions as the server. | |
| int32_t | HITLS_ReadHasPending (const HITLS_Ctx *ctx, bool *isPending) |
| Check the HiTLS object in the read cache. (including processed and unprocessed data, excluding the network layer) Whether there is data | |
| uint32_t | HITLS_GetReadPendingBytes (const HITLS_Ctx *ctx) |
| Obtain the number of bytes of application data to be read from the current record from the HiTLS object. | |
| int32_t | HITLS_GetPeerSignScheme (const HITLS_Ctx *ctx, HITLS_SignHashAlgo *peerSignScheme) |
| Obtain the signature hash algorithm used by the peer end. | |
| int32_t | HITLS_GetLocalSignScheme (const HITLS_Ctx *ctx, HITLS_SignHashAlgo *localSignScheme) |
| Obtain the signature hash algorithm used by the local end. | |
| int32_t | HITLS_GetSharedSigAlgs (const HITLS_Ctx *ctx, int32_t idx, uint16_t *signatureScheme, int32_t *keyType, int32_t *paraId) |
| Get shared signature algorithms (negotiated) | |
| int32_t | HITLS_SetEcGroups (HITLS_Ctx *ctx, uint16_t *lst, uint32_t groupSize) |
| Set the group supported by the hitls object. | |
| int32_t | HITLS_SetGroupList (HITLS_Ctx *ctx, const char *groups, uint32_t groupNamesLen) |
| Set the group supported during key exchange, the group supported by HiTLS can be queried in HITLS_NamedGroup. | |
| int32_t | HITLS_SetSigalgsList (HITLS_Ctx *ctx, const uint16_t *signAlgs, uint16_t signAlgsSize) |
| Set the signature algorithm supported by the hitls object. | |
| int32_t | HITLS_SetEcPointFormats (HITLS_Ctx *ctx, const uint8_t *pointFormats, uint32_t pointFormatsSize) |
| Set the EC point format of the hitls. | |
| int32_t | HITLS_SetClientVerifySupport (HITLS_Ctx *ctx, bool support) |
| Set whether to verify the client certificate. | |
| int32_t | HITLS_SetNoClientCertSupport (HITLS_Ctx *ctx, bool support) |
| Set whether to support the function without the client certificate, Takes effect only when the client certificate is verified. Client: This setting has no impact Server: When an NULL certificate is received from the client, indicates whether the certificate passes the verification, the verification fails by default. | |
| int32_t | HITLS_SetPostHandshakeAuthSupport (HITLS_Ctx *ctx, bool support) |
| Set whether to support post-handshake AUTH. | |
| int32_t | HITLS_SetVerifyNoneSupport (HITLS_Ctx *ctx, bool support) |
| Set whether to support do not proceed dual-ended verification. | |
| int32_t | HITLS_SetClientOnceVerifySupport (HITLS_Ctx *ctx, bool support) |
| Set whether the client certificate can be requested only once. | |
| const HITLS_Config * | HITLS_GetConfig (const HITLS_Ctx *ctx) |
| Obtain the value of hitlsConfig. | |
| HITLS_Config * | HITLS_GetGlobalConfig (const HITLS_Ctx *ctx) |
| Obtain the point of GlobalConfig | |
| int32_t | HITLS_ClearTLS13CipherSuites (HITLS_Ctx *ctx) |
| Clears the configured TLS1.3 cipher suite. | |
| int32_t | HITLS_SetCipherSuites (HITLS_Ctx *ctx, const uint16_t *cipherSuites, uint32_t cipherSuitesSize) |
| Set the supported cipher suites. The sequence of the cipher suites affects the priority of the selected cipher suites. The cipher suites with the highest priority are selected first. | |
| int32_t | HITLS_GetCipherSuites (HITLS_Ctx *ctx, uint16_t *data, uint32_t dataLen, uint32_t *cipherSuitesSize) |
| Get the supported cipher suites array. | |
| int32_t | HITLS_GetClientCipherSuites (HITLS_Ctx *ctx, uint16_t *data, uint32_t dataLen, uint32_t *cipherSuitesSize) |
| Get the received cipher suites array from the client. | |
| const HITLS_Cipher * | HITLS_GetCurrentCipher (const HITLS_Ctx *ctx) |
| Obtain the negotiated cipher suite pointer. | |
| HITLS_CIPHER_List * | HITLS_GetSupportedCiphers (const HITLS_Ctx *ctx) |
| Obtain the supported cipher suites list for HITLS_Ctx. | |
| int32_t | HITLS_GetHsRandom (const HITLS_Ctx *ctx, uint8_t *out, uint32_t *outlen, bool isClient) |
| Obtain the random number of the client and server during the handshake. | |
| int32_t | HITLS_GetHandShakeState (const HITLS_Ctx *ctx, uint32_t *state) |
| Obtain the current handshake status. | |
| const char * | HITLS_GetStateString (uint32_t state) |
| Obtain the handshake status character string. | |
| int32_t | HITLS_IsHandShaking (const HITLS_Ctx *ctx, bool *isHandShaking) |
| Check whether a handshake is being performed. | |
| int32_t | HITLS_GetRenegotiationSupport (const HITLS_Ctx *ctx, bool *isSupportRenegotiation) |
| Obtain whether renegotiation is supported. | |
| int32_t | HITLS_IsBeforeHandShake (const HITLS_Ctx *ctx, bool *isBefore) |
| Check whether the handshake has not been performed. | |
| int32_t | HITLS_SetLinkMtu (HITLS_Ctx *ctx, uint16_t linkMtu) |
| Set the MTU of Data Link layer. | |
| int32_t | HITLS_SetMtu (HITLS_Ctx *ctx, uint16_t mtu) |
| Set the MTU of a path. | |
| int32_t | HITLS_SetNoQueryMtu (HITLS_Ctx *ctx, bool noQueryMtu) |
| Set the option that don't query mtu from the bio. | |
| int32_t | HITLS_GetNeedQueryMtu (HITLS_Ctx *ctx, bool *needQueryMtu) |
| Querying whether the EMSGSIZE error occur and mtu need be modified | |
| int32_t | HITLS_GetClientVersion (const HITLS_Ctx *ctx, uint16_t *clientVersion) |
| Obtain the version number set by the client in ClientHello. | |
| int32_t | HITLS_DoHandShake (HITLS_Ctx *ctx) |
| The client/server starts handshake. | |
| int32_t | HITLS_IsClient (const HITLS_Ctx *ctx, bool *isClient) |
| Check whether the current end is client. | |
| int32_t | HITLS_KeyUpdate (HITLS_Ctx *ctx, uint32_t updateType) |
| Set the keyupdate type of the current context and send the keyupdate message. | |
| int32_t | HITLS_GetKeyUpdateType (HITLS_Ctx *ctx) |
| Return the keyupdate type of the current context. | |
| int32_t | HITLS_GetSharedGroup (const HITLS_Ctx *ctx, int32_t nmatch, uint16_t *groupId) |
| Obtain the supported peer group or the number of supported peer groups of the nth match. nmatch Value range: - 1 or a positive integer This function can be called only after negotiation and can be called only by the server. If nmatch is a positive integer, check the intersection of groups on the client and server, and return the nmatch group in the intersection by groupId. If the value of nmatch is - 1, the number of intersection groups on the client and server is returned based on groupId. | |
| int32_t | HITLS_SetDtlsTimerCb (HITLS_Ctx *ctx, HITLS_DtlsTimerCb cb) |
| Set the DTLS timeout interval callback. | |
| int32_t | HITLS_GetVersionSupport (const HITLS_Ctx *ctx, uint32_t *version) |
| Obtain the supported version number. | |
| int32_t | HITLS_SetVersionSupport (HITLS_Ctx *ctx, uint32_t version) |
| Set the supported version number. | |
| int32_t | HITLS_SetVersion (HITLS_Ctx *ctx, uint32_t minVersion, uint32_t maxVersion) |
| Set the supported version number range. | |
| int32_t | HITLS_SetVersionForbid (HITLS_Ctx *ctx, uint32_t noVersion) |
| Set the version number to be disabled. | |
| int32_t | HITLS_SetNeedCheckPmsVersion (HITLS_Ctx *ctx, bool needCheck) |
| Sets whether to verify the version in the premaster secret. | |
| int32_t | HITLS_SetQuietShutdown (HITLS_Ctx *ctx, int32_t mode) |
| Set the silent disconnection mode. | |
| int32_t | HITLS_GetQuietShutdown (const HITLS_Ctx *ctx, int32_t *mode) |
| Obtain the current silent disconnection mode. | |
| int32_t | HITLS_SetDhAutoSupport (HITLS_Ctx *ctx, bool support) |
| Sets whether to support the function of automatically selecting DH parameters. If the value is true, the DH parameter is automatically selected based on the length of the certificate private key. If the value is false, the DH parameter needs to be set. | |
| int32_t | HITLS_SetTmpDh (HITLS_Ctx *ctx, HITLS_CRYPT_Key *dhPkey) |
| Set the DH parameter specified by the user. | |
| int32_t | HITLS_SetTmpDhCb (HITLS_Ctx *ctx, HITLS_DhTmpCb callback) |
| Set the TmpDh callback function. | |
| int32_t | HITLS_SetRecordPaddingCb (HITLS_Ctx *ctx, HITLS_RecordPaddingCb callback) |
| Sets the RecordPadding callback. | |
| HITLS_RecordPaddingCb | HITLS_GetRecordPaddingCb (HITLS_Ctx *ctx) |
| Obtains the RecordPadding callback function. | |
| int32_t | HITLS_SetRecordPaddingCbArg (HITLS_Ctx *ctx, void *arg) |
| Sets the parameters arg required by the RecordPadding callback function. | |
| void * | HITLS_GetRecordPaddingCbArg (HITLS_Ctx *ctx) |
| Obtains the parameter arg required by the RecordPadding callback function. | |
| int32_t | HITLS_GetPeerFinishVerifyData (const HITLS_Ctx *ctx, void *buf, uint32_t bufLen, uint32_t *dataLen) |
| Obtain the verification data and length of the peer end based on the received finished message. | |
| int32_t | HITLS_SetCheckKeyUsage (HITLS_Ctx *ctx, bool isCheck) |
| Disables the verification of keyusage in the certificate. This function is enabled by default. | |
| int32_t | HITLS_GetFinishVerifyData (const HITLS_Ctx *ctx, void *buf, uint32_t bufLen, uint32_t *dataLen) |
| Obtain the verification data and length of the local end based on the sent finished message. | |
| int32_t | HITLS_GetSecureRenegotiationSupport (const HITLS_Ctx *ctx, bool *isSecureRenegotiation) |
| Obtains whether security renegotiation is supported. | |
| int32_t | HITLS_Renegotiate (HITLS_Ctx *ctx) |
| Perform renegotiation. | |
| int32_t | HITLS_GetRenegotiationState (const HITLS_Ctx *ctx, bool *isRenegotiationState) |
| Obtain the current is whether in the renegotiation state. | |
| int32_t | HITLS_GetRwstate (const HITLS_Ctx *ctx, uint8_t *rwstate) |
| Obtain the current internal status. | |
| int32_t | HITLS_GetClientVerifySupport (HITLS_Ctx *ctx, bool *isSupport) |
| Check whether the client certificate can be verified. | |
| int32_t | HITLS_GetNoClientCertSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Check whether no client certificate is supported, This command is valid only when client certificate verification is enabled. | |
| int32_t | HITLS_GetPostHandshakeAuthSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Query whether post-handshake AUTH is supported | |
| int32_t | HITLS_GetVerifyNoneSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Query if support is available for not performing dual-end verification. | |
| int32_t | HITLS_GetClientOnceVerifySupport (HITLS_Ctx *ctx, bool *isSupport) |
| Query whether the client certificate can be requested only once. | |
| int32_t | HITLS_ClearRenegotiationNum (HITLS_Ctx *ctx, uint32_t *renegotiationNum) |
| Clears the renegotiation count. | |
| int32_t | HITLS_GetNegotiateGroup (const HITLS_Ctx *ctx, uint16_t *group) |
| Obtain the negotiated group information. | |
| int32_t | HITLS_SetModeSupport (HITLS_Ctx *ctx, uint32_t mode) |
| Set the function to support the specified feature. | |
| int32_t | HITLS_ClearModeSupport (HITLS_Ctx *ctx, uint32_t mode) |
| Function to clear the specified feature. | |
| int32_t | HITLS_GetModeSupport (const HITLS_Ctx *ctx, uint32_t *mode) |
| Obtains the functional characteristics mode in the config. | |
| int32_t | HITLS_SetEncryptThenMac (HITLS_Ctx *ctx, bool encryptThenMacType) |
| Setting the Encrypt-Then-Mac mode. | |
| int32_t | HITLS_GetEncryptThenMac (const HITLS_Ctx *ctx, bool *encryptThenMacType) |
| Obtains the Encrypt-Then-Mac type | |
| int32_t | HITLS_SetServerName (HITLS_Ctx *ctx, uint8_t *serverName, uint32_t serverNameStrlen) |
| Setting the value of server_name. | |
| int32_t | HITLS_SetCipherServerPreference (HITLS_Ctx *ctx, bool isSupport) |
| The algorithm suite can be preferentially selected from the algorithm list supported by the server. | |
| int32_t | HITLS_GetCipherServerPreference (const HITLS_Ctx *ctx, bool *isSupport) |
| Obtains whether the current cipher suite supports preferential selection from the list of algorithms supported by the server. | |
| int32_t | HITLS_SetRenegotiationSupport (HITLS_Ctx *ctx, bool isSupport) |
| Sets whether to support renegotiation. | |
| int32_t | HITLS_SetClientRenegotiateSupport (HITLS_Ctx *ctx, bool isSupport) |
| Set whether to allow a renegotiate request from the client | |
| int32_t | HITLS_SetLegacyRenegotiateSupport (HITLS_Ctx *ctx, bool isSupport) |
| Set whether to abort handshake when server doesn't support SecRenegotiation | |
| int32_t | HITLS_SetSessionTicketSupport (HITLS_Ctx *ctx, bool isSupport) |
| Sets whether to support session tickets. | |
| int32_t | HITLS_GetSessionTicketSupport (const HITLS_Ctx *ctx, bool *isSupport) |
| Check whether the session ticket is supported. | |
| int32_t | HITLS_SetDtlsCookieExangeSupport (HITLS_Ctx *ctx, bool isSupport) |
| Sets whether to perform cookie exchange in the dtls. | |
| int32_t | HITLS_GetDtlsCookieExangeSupport (const HITLS_Ctx *ctx, bool *isSupport) |
| Querying whether the DTLS performs cookie exchange. | |
| int32_t | HITLS_SetFlightTransmitSwitch (HITLS_Ctx *ctx, bool isEnable) |
| Sets whether to send handshake messages by flight distance. | |
| int32_t | HITLS_GetFlightTransmitSwitch (const HITLS_Ctx *ctx, bool *isEnable) |
| Obtains the status of whether to send handshake information according to the flight distance. | |
| int32_t | HITLS_SetEmptyRecordsNum (HITLS_Ctx *ctx, uint32_t emptyNum) |
| set the max empty records number can be received | |
| int32_t | HITLS_SetMaxSendFragment (HITLS_Ctx *ctx, uint16_t maxSendFragment) |
| set the max send fragment to restrict the amount of plaintext bytes in any record | |
| int32_t | HITLS_GetMaxSendFragment (const HITLS_Ctx *ctx, uint16_t *maxSendFragment) |
| Obtain the max send fragment to restrict the amount of plaintext bytes in any record | |
| int32_t | HITLS_SetRecInbufferSize (HITLS_Ctx *ctx, uint32_t recInbufferSize) |
| Set the rec inbuffer inital size | |
| int32_t | HITLS_GetRecInbufferSize (const HITLS_Ctx *ctx, uint32_t *recInbufferSize) |
| Obtain the rec inbuffer inital size | |
| int32_t | HITLS_GetEmptyRecordsNum (const HITLS_Ctx *ctx, uint32_t *emptyNum) |
| Obtain the max empty records number can be received | |
| int32_t | HITLS_SetMaxCertList (HITLS_Ctx *ctx, uint32_t maxSize) |
| Sets the maximum size of the certificate chain that can be sent from the peer end. | |
| int32_t | HITLS_GetMaxCertList (const HITLS_Ctx *ctx, uint32_t *maxSize) |
| Obtains the maximum size of the certificate chain that can be sent by the peer end. | |
| int32_t | HITLS_ExportKeyingMaterial (HITLS_Ctx *ctx, uint8_t *out, size_t outLen, const char *label, size_t labelLen, const uint8_t *context, size_t contextLen, int32_t useContext) |
| This API is designed for upper layer applications to export key materials based on RFC5705 (version < tls1.2) or RFC8446 (tls1.3). | |
| int32_t | HITLS_VerifyClientPostHandshake (HITLS_Ctx *ctx) |
| This interface is valid only on the server. When the post-handshake command is configured, the client identity is verified through this interface. | |
| int32_t | HITLS_SetKeepPeerCertificate (HITLS_Ctx *ctx, bool isKeepPeerCert) |
| Set whether to save the peer certificate. | |
| int32_t | HITLS_SetRecordSizeLimit (HITLS_Ctx *ctx, uint16_t recordSize) |
| The default record size limit is 0 to unsupport the record size limit extension (RFC 8449). If negotiated, it is used only to limit the size of records sent by the peer in the receive direction. However, the record size sent to the peer is limited by the record size limit value of the peer. | |
| int32_t | HITLS_GetRecordSizeLimit (HITLS_Ctx *ctx, uint16_t *recordSize) |
| Obtains the record size limit value of ctx. | |
| int32_t | HITLS_ClientHelloGetLegacyVersion (HITLS_Ctx *ctx, uint16_t *version) |
| Obtain the legacy version from client hello. | |
| int32_t | HITLS_ClientHelloGetRandom (HITLS_Ctx *ctx, uint8_t **out, uint8_t *outlen) |
| Obtain the random value from client hello. | |
| int32_t | HITLS_ClientHelloGetSessionID (HITLS_Ctx *ctx, uint8_t **out, uint8_t *outlen) |
| Obtain the session ID from client hello. | |
| int32_t | HITLS_ClientHelloGetCiphers (HITLS_Ctx *ctx, uint16_t **out, uint16_t *outlen) |
| Obtain the cipher suites from client hello. | |
| int32_t | HITLS_ClientHelloGetExtensionsPresent (HITLS_Ctx *ctx, uint16_t **out, uint8_t *outlen) |
| Obtain the all extension types from client hello. | |
| int32_t | HITLS_ClientHelloGetExtension (HITLS_Ctx *ctx, uint16_t type, uint8_t **out, uint32_t *outlen) |
| Obtain a specific extension from client hello. | |
| int32_t | HITLS_DtlsProcessTimeout (HITLS_Ctx *ctx) |
| Handle the timeout of sending and receiving DTLS messages. | |
| int32_t | HITLS_DtlsGetTimeout (HITLS_Ctx *ctx, uint64_t *remainTimeOut) |
| Get the remaining timeout time for timeout retransmission. | |
| int32_t | HITLS_SetMiddleBoxCompat (HITLS_Ctx *ctx, bool isMiddleBox) |
| Sets whether to support middle box compat mode. | |
| int32_t | HITLS_GetMiddleBoxCompat (HITLS_Ctx *ctx, bool *isMiddleBox) |
| Obtain whether middle box compat mode is supported. | |
| int32_t | HITLS_GetOutPendingSize (const HITLS_Ctx *ctx, uint32_t *size) |
| Obtain the record out buffer remaining size | |
| int32_t | HITLS_Flush (HITLS_Ctx *ctx) |
| Flush the record out buffer | |
| int32_t | HITLS_SetExtendedMasterSecretSupport (HITLS_Ctx *ctx, bool support) |
| Sets whether to forcibly support extended master keys. | |
| int32_t | HITLS_GetExtendedMasterSecretSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Query whether extended master keys are supported. | |
| int32_t | HITLS_SetExtendedMasterSecretMode (HITLS_Ctx *ctx, int32_t mode) |
| Set extended master secret mode. | |
| int32_t | HITLS_GetExtendedMasterSecretMode (HITLS_Ctx *ctx, int32_t *mode) |
| Get extended master secret mode. | |
| int32_t | HITLS_SetResumptionOnRenegoSupport (HITLS_Ctx *ctx, bool support) |
| Set whether to support session restoration during renegotiation. By default, session restoration is not supported. | |
| int32_t | HITLS_GetResumptionOnRenegoSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Get whether to support session restoration during renegotiation. By default, session restoration is not supported. | |
| int32_t | HITLS_GetClientRenegotiateSupport (HITLS_Ctx *ctx, bool *isSupport) |
| Get whether to allow a renegotiate request from the client | |
| int32_t | HITLS_CFG_SetMiddleBoxCompat (HITLS_Config *config, bool isMiddleBox) |
| Sets whether to support middle box compat mode. | |
| int32_t | HITLS_CFG_GetMiddleBoxCompat (HITLS_Config *config, bool *isMiddleBox) |
| Obtain whether middle box compat mode is supported. | |
| int32_t HITLS_Accept | ( | HITLS_Ctx * | ctx | ) |
The server waits for the client to start handshake.
The server waits for the client to initiate the handshake. The UIO object must be created and bound to the HiTLS context.
HITLS_Accept is designed for non-blocking interfaces. If the handshake cannot be continued, the system returns. The return value is not success. If the return value is HITLS_REC_NORMAL_RECV_BUF_EMPTY or HITLS_REC_NORMAL_IO_BUSY, no fatal error occurs. Problems such as network congestion or network delay may occur. You can continue to call HITLS_Accept. Note that if the UIO is blocked, the HITLS_Accept will also be blocked, but the processing of the returned value is the same.
| ctx | [IN] TLS connection handle. |
| HITLS_SUCCESS,the | handshake is successful. |
| HITLS_REC_NORMAL_RECV_BUF_EMPTY,record | The receiving buffer is NULL and the handshake can continue. |
| HITLS_REC_NORMAL_IO_BUSY,the | network I/O is busy and needs to wait for the next sending. You can continue the handshake. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_CFG_GetMiddleBoxCompat | ( | HITLS_Config * | config, |
| bool * | isMiddleBox ) |
Obtain whether middle box compat mode is supported.
| config | [IN] Config context |
| isMiddleBox | [OUT] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_CFG_SetMiddleBoxCompat | ( | HITLS_Config * | config, |
| bool | isMiddleBox ) |
Sets whether to support middle box compat mode.
| config | [OUT] Config context |
| isMiddleBox | [IN] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_Clear | ( | HITLS_Ctx * | ctx | ) |
Reset the TLS handle to allow it to be used for another connection.
| ctx | [IN] TLS connection handle. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_ClearModeSupport | ( | HITLS_Ctx * | ctx, |
| uint32_t | mode ) |
Function to clear the specified feature.
| ctx | [OUT] TLS Connection Handle |
| mode | [IN] Mode features to clear. |
| HITLS_NULL_INPUT,the | input parameter pointer is null. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_ClearRenegotiationNum | ( | HITLS_Ctx * | ctx, |
| uint32_t * | renegotiationNum ) |
Clears the renegotiation count.
| ctx | [IN] hitls context. |
| renegotiationNum | [OUT] Number of incoming renegotiations. |
| int32_t HITLS_ClearTLS13CipherSuites | ( | HITLS_Ctx * | ctx | ) |
Clears the configured TLS1.3 cipher suite.
| ctx | [IN] TLS connection handle. |
| int32_t HITLS_ClientHelloGetCiphers | ( | HITLS_Ctx * | ctx, |
| uint16_t ** | out, | ||
| uint16_t * | outlen ) |
Obtain the cipher suites from client hello.
| ctx | [IN] TLS connection handle. |
| out | [OUT] Pointer to the output buffer for cipher suites. |
| outlen | [OUT] Length of the output buffer. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_ClientHelloGetExtension | ( | HITLS_Ctx * | ctx, |
| uint16_t | type, | ||
| uint8_t ** | out, | ||
| uint32_t * | outlen ) |
Obtain a specific extension from client hello.
| ctx | [IN] TLS connection handle. |
| type | [IN] Type of the extension to be obtained. |
| out | [OUT] Pointer to the output buffer for the extension. |
| outlen | [OUT] Length of the output buffer. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_ClientHelloGetExtensionsPresent | ( | HITLS_Ctx * | ctx, |
| uint16_t ** | out, | ||
| uint8_t * | outlen ) |
Obtain the all extension types from client hello.
| ctx | [IN] TLS connection handle. |
| out | [OUT] Pointer to the output buffer for all extensions. |
| outlen | [OUT] Length of the output buffer. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_ClientHelloGetLegacyVersion | ( | HITLS_Ctx * | ctx, |
| uint16_t * | version ) |
Obtain the legacy version from client hello.
| ctx | [IN] TLS connection handle. |
| version | [OUT] Pointer to the output buffer for legacy version. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_ClientHelloGetRandom | ( | HITLS_Ctx * | ctx, |
| uint8_t ** | out, | ||
| uint8_t * | outlen ) |
Obtain the random value from client hello.
| ctx | [IN] TLS connection handle. |
| out | [OUT] Pointer to the output buffer for random value. |
| outlen | [IN] Length of the output buffer. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_ClientHelloGetSessionID | ( | HITLS_Ctx * | ctx, |
| uint8_t ** | out, | ||
| uint8_t * | outlen ) |
Obtain the session ID from client hello.
| ctx | [IN] TLS connection handle. |
| out | [OUT] Pointer to the output buffer for session ID. |
| outlen | [OUT] Length of the output buffer. |
| HITLS_SUCCESS,if | successful. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_Close | ( | HITLS_Ctx * | ctx | ) |
Close the TLS connection.
| ctx | [IN] TLS connection handle. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_Connect | ( | HITLS_Ctx * | ctx | ) |
The client starts the handshake with the TLS server.
Starting the handshake with the TLS server using HITLS_Connect. The UIO object must be created and bound to the HiTLS context. HITLS_Connect is designed as a non-blocking interface. If the handshake cannot be continued, the returned value will not be HITLS_SUCCESS. If the return value is HITLS_REC_NORMAL_RECV_BUF_EMPTY or HITLS_REC_NORMAL_IO_BUSY, no fatal error occurs. Problems such as network congestion or network delay may occur. You can continue to call HITLS_Connect. Note that if UIO is blocked, HITLS_Connect will also block, but the return value is processed in the same way.
| ctx | [IN] TLS connection handle. |
| HITLS_SUCCESS | |
| HITLS_REC_NORMAL_RECV_BUF_EMPTY,record | The receiving buffer is NULL and the handshake can be continued. |
| HITLS_REC_NORMAL_IO_BUSY,the | network I/O is busy and needs to wait for the next sending. You can continue the handshake. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_DoHandShake | ( | HITLS_Ctx * | ctx | ) |
The client/server starts handshake.
| ctx | [IN] TLS connection handle |
| int32_t HITLS_DtlsGetTimeout | ( | HITLS_Ctx * | ctx, |
| uint64_t * | remainTimeOut ) |
Get the remaining timeout time for timeout retransmission.
| ctx | [IN] TLS Connection Handle |
| remainTimeOut | [OUT] remaining timeout time for timeout retransmission, unit: us |
| HITLS_SUCCESS,if | successful. |
| HITLS_MSG_HANDLE_ERR_WITHOUT_TIMEOUT_ACTION,Indicates | non UDP links or absence of timeout behavior. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_DtlsProcessTimeout | ( | HITLS_Ctx * | ctx | ) |
Handle the timeout of sending and receiving DTLS messages.
| ctx | [IN] TLS Connection Handle |
| HITLS_SUCCESS,if | retransmit the message successful. |
| HITLS_MSG_HANDLE_DTLS_RETRANSMIT_NOT_TIMEOUT,It | hasn't timed out yet. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_ExportKeyingMaterial | ( | HITLS_Ctx * | ctx, |
| uint8_t * | out, | ||
| size_t | outLen, | ||
| const char * | label, | ||
| size_t | labelLen, | ||
| const uint8_t * | context, | ||
| size_t | contextLen, | ||
| int32_t | useContext ) |
This API is designed for upper layer applications to export key materials based on RFC5705 (version < tls1.2) or RFC8446 (tls1.3).
| ctx | [IN] TLS connection handle. |
| out | [OUT] Cache for receiving the exported key. |
| outLen | [IN/OUT] Length of the exported key. |
| label | [IN] Key export parameter. |
| labelLen | [IN] Length of the key export parameter. |
| context | [IN] Key export parameter. |
| contextLen | [IN] Length of the key export parameter. |
| useContext | [IN] Whether to use the context field. |
| HITLS_INVALID_INPUT,invalid | input parameter. |
| HITLS_SUCCESS,if | successful. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_Flush | ( | HITLS_Ctx * | ctx | ) |
Flush the record out buffer
| ctx | [IN] TLS connection handle |
| HITLS_SUCCESS | Out buffer is empty or flush success |
| HITLS_REC_NORMAL_IO_BUSY | Out buffer is not empty, but the IO operation is busy |
| void HITLS_Free | ( | HITLS_Ctx * | ctx | ) |
Release the TLS connection.
| ctx | [IN] TLS connection handle. |
| int32_t HITLS_GetCipherServerPreference | ( | const HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Obtains whether the current cipher suite supports preferential selection from the list of algorithms supported by the server.
| ctx | [IN] TLS connection handle. |
| isSupport | [OUT] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetCipherSuites | ( | HITLS_Ctx * | ctx, |
| uint16_t * | data, | ||
| uint32_t | dataLen, | ||
| uint32_t * | cipherSuitesSize ) |
Get the supported cipher suites array.
| ctx | [IN] TLS connection handle. |
| data | [OUT] Array for storing cipher suites. |
| dataLen | [IN] Array length. |
| cipherSuitesSize | [OUT] cipher suite array length. |
| int32_t HITLS_GetClientCipherSuites | ( | HITLS_Ctx * | ctx, |
| uint16_t * | data, | ||
| uint32_t | dataLen, | ||
| uint32_t * | cipherSuitesSize ) |
Get the received cipher suites array from the client.
| ctx | [IN] TLS connection handle. |
| data | [OUT] Array for storing cipher suites. |
| dataLen | [IN] Array length. |
| cipherSuitesSize | [OUT] cipher suite array length. |
| int32_t HITLS_GetClientOnceVerifySupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Query whether the client certificate can be requested only once.
| ctx | [IN] TLS Connection Handle. |
| isSupport | [OUT] Indicates whether the client certificate can be requested only once. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetClientRenegotiateSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Get whether to allow a renegotiate request from the client
| ctx | [IN] TLS connection handle. |
| isSupport | [OUT] Indicates whether to allow a renegotiate request from the client |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_GetClientVerifySupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Check whether the client certificate can be verified.
| ctx | [IN] TLS connection Handle. |
| isSupport | [OUT] Indicates whether to verify the client certificate. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetClientVersion | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | clientVersion ) |
Obtain the version number set by the client in ClientHello.
| ctx | [IN] TLS connection handle |
| clientVersion | [OUT] Obtained version number |
| const HITLS_Config * HITLS_GetConfig | ( | const HITLS_Ctx * | ctx | ) |
Obtain the value of hitlsConfig.
| ctx | [IN] TLS connection handle |
| const HITLS_Cipher * HITLS_GetCurrentCipher | ( | const HITLS_Ctx * | ctx | ) |
Obtain the negotiated cipher suite pointer.
| ctx | [IN] TLS connection handle |
| int32_t HITLS_GetDtlsCookieExangeSupport | ( | const HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Querying whether the DTLS performs cookie exchange.
| ctx | [IN] TLS connection handle. |
| isSupport | [IN] Indicates whether to perform cookie exchange. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetEmptyRecordsNum | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | emptyNum ) |
Obtain the max empty records number can be received
| ctx | [IN] TLS connection handle. |
| emptyNum | [OUT] Indicates the max number of empty records can be received |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetEncryptThenMac | ( | const HITLS_Ctx * | ctx, |
| bool * | encryptThenMacType ) |
Obtains the Encrypt-Then-Mac type
| ctx | [IN] TLS connection Handle. |
| encryptThenMacType | [OUT] Current Encrypt-Then-Mac mode. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetErrorCode | ( | const HITLS_Ctx * | ctx | ) |
Obtain the error value of the HiTLS link.
| ctx | [OUT] TLS connection handle |
| Link | error value |
| int32_t HITLS_GetExtendedMasterSecretMode | ( | HITLS_Ctx * | ctx, |
| int32_t * | mode ) |
Get extended master secret mode.
| ctx | [IN] TLS connection handle |
| mode | [OUT] EMS mode. See HITLS_EMS_MODE_*. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,if | ctx or mode is NULL. |
| int32_t HITLS_GetExtendedMasterSecretSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Query whether extended master keys are supported.
| ctx | [IN] TLS connection handle |
| isSupport | [OUT] Indicates whether to support the extended master key. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is NULL. |
| int32_t HITLS_GetFinishVerifyData | ( | const HITLS_Ctx * | ctx, |
| void * | buf, | ||
| uint32_t | bufLen, | ||
| uint32_t * | dataLen ) |
Obtain the verification data and length of the local end based on the sent finished message.
| ctx | [IN] TLS context |
| buf | [OUT] verify data |
| bufLen | [IN] Length of the buffer to be obtained |
| dataLen | [OUT] Indicates the actual length of the buffer |
| int32_t HITLS_GetFlightTransmitSwitch | ( | const HITLS_Ctx * | ctx, |
| bool * | isEnable ) |
Obtains the status of whether to send handshake information according to the flight distance.
| ctx | [IN] TLS connection handle. |
| isEnable | [OUT] Indicates whether to send handshake information by flight distance |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| HITLS_Config * HITLS_GetGlobalConfig | ( | const HITLS_Ctx * | ctx | ) |
Obtain the point of GlobalConfig
| ctx | [IN] TLS connection handle |
| int32_t HITLS_GetHandShakeState | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | state ) |
Obtain the current handshake status.
| ctx | [IN] TLS connection handle |
| state | [OUT] Current handshake status |
| int32_t HITLS_GetHsRandom | ( | const HITLS_Ctx * | ctx, |
| uint8_t * | out, | ||
| uint32_t * | outlen, | ||
| bool | isClient ) |
Obtain the random number of the client and server during the handshake.
| ctx | [IN] TLS connection handle |
| out | [OUT] Random number obtained |
| outlen | [OUT] Length of the input parameter out. If the length is greater than the maximum random number length, the value will be changed. |
| isClient | [IN] True, obtain the random number of the client. False, obtain the random number of the server. |
| int32_t HITLS_GetKeyUpdateType | ( | HITLS_Ctx * | ctx | ) |
Return the keyupdate type of the current context.
| ctx | [IN] TLS connection handle |
| KeyUpdateType | in ctx |
| NULL,the | input parameter pointer is null. |
| int32_t HITLS_GetLocalSignScheme | ( | const HITLS_Ctx * | ctx, |
| HITLS_SignHashAlgo * | localSignScheme ) |
Obtain the signature hash algorithm used by the local end.
| ctx | [IN] TLS connection handle |
| localSignScheme | [OUT] Local signature hash algorithm |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_GetMaxCertList | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | maxSize ) |
Obtains the maximum size of the certificate chain that can be sent by the peer end.
| ctx | [IN] TLS connection handle. |
| maxSize | [OUT] Maximum size of the certificate chain that can be sent from the peer end. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetMaxProtoVersion | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | maxVersion ) |
Obtain the latest protocol version.
| ctx | [IN] TLS object |
| minVersion | [OUT] Latest protocol version supported |
| int32_t HITLS_GetMaxSendFragment | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | maxSendFragment ) |
Obtain the max send fragment to restrict the amount of plaintext bytes in any record
| ctx | [IN] TLS connection handle. |
| maxSendFragment | [OUT] Indicates the max send fragment |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetMaxWriteSize | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | len ) |
Obtain the maximum writable (plaintext) length.
| ctx | [OUT] TLS connection handle. |
| len | [OUT] Maximum writable plaintext length (within 16 KB) |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_GetMiddleBoxCompat | ( | HITLS_Ctx * | ctx, |
| bool * | isMiddleBox ) |
Obtain whether middle box compat mode is supported.
| ctx | [IN] TLS connection handle. |
| isMiddleBox | [OUT] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetMinProtoVersion | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | minVersion ) |
Obtain the latest protocol version.
| ctx | [IN] TLS object |
| maxVersion | [OUT] Latest protocol version supported |
| int32_t HITLS_GetModeSupport | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | mode ) |
Obtains the functional characteristics mode in the config.
| ctx | [IN] TLS Connection Handle. |
| mode | [OUT] Output parameter for obtaining the mode. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetNeedQueryMtu | ( | HITLS_Ctx * | ctx, |
| bool * | needQueryMtu ) |
Querying whether the EMSGSIZE error occur and mtu need be modified
| ctx | [IN] TLS connection handle. |
| needQueryMtu | [IN] Indicates whether the EMSGSIZE error occur and mtu need be modified |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetNegotiatedVersion | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | version ) |
Obtain the HiTLS negotiation version.
| ctx | [IN] TLS object |
| version | [OUT] Negotiated version |
| int32_t HITLS_GetNegotiateGroup | ( | const HITLS_Ctx * | ctx, |
| uint16_t * | group ) |
Obtain the negotiated group information.
| ctx | [IN] TLS Connection Handle. |
| group | [OUT] Negotiated group information. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetNoClientCertSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Check whether no client certificate is supported, This command is valid only when client certificate verification is enabled.
| ctx | [IN] TLS Connection Handle. |
| isSupport | [OUT] Whether no client certificate is supported. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetOutPendingSize | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | size ) |
Obtain the record out buffer remaining size
| ctx | [IN] TLS connection handle |
| size | [OUT] record out buffer remaining size |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_GetPeerFinishVerifyData | ( | const HITLS_Ctx * | ctx, |
| void * | buf, | ||
| uint32_t | bufLen, | ||
| uint32_t * | dataLen ) |
Obtain the verification data and length of the peer end based on the received finished message.
| ctx | [IN] TLS context |
| buf | [OUT] verify data |
| bufLen | [IN] Length of the buffer to be obtained |
| dataLen | [OUT] Actual length of the buf |
| int32_t HITLS_GetPeerSignScheme | ( | const HITLS_Ctx * | ctx, |
| HITLS_SignHashAlgo * | peerSignScheme ) |
Obtain the signature hash algorithm used by the peer end.
| ctx | [IN] TLS connection handle |
| peerSignScheme | [OUT] Peer signature hash algorithm |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_GetPostHandshakeAuthSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Query whether post-handshake AUTH is supported
| ctx | [IN] TLS connection Handle. |
| isSupport | [OUT] indicates whether to support post-handshake AUTH. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetQuietShutdown | ( | const HITLS_Ctx * | ctx, |
| int32_t * | mode ) |
Obtain the current silent disconnection mode.
| ctx | [IN] TLS connection handle |
| mode | [OUT] Mode type. |
| uint32_t HITLS_GetReadPendingBytes | ( | const HITLS_Ctx * | ctx | ) |
Obtain the number of bytes of application data to be read from the current record from the HiTLS object.
| ctx | [IN] TLS connection handle |
| Number | of bytes of application data that can be read. |
Obtain the UIO object of the read data.
| ctx | [IN] TLS object |
| int32_t HITLS_GetRecInbufferSize | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | recInbufferSize ) |
Obtain the rec inbuffer inital size
| ctx | [IN] TLS connection handle. |
| recInbufferSize | [OUT] Indicates the rec inbuffer inital size |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| HITLS_RecordPaddingCb HITLS_GetRecordPaddingCb | ( | HITLS_Ctx * | ctx | ) |
Obtains the RecordPadding callback function.
| ctx | [IN/OUT] TLS Connection Handle |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| void * HITLS_GetRecordPaddingCbArg | ( | HITLS_Ctx * | ctx | ) |
Obtains the parameter arg required by the RecordPadding callback function.
| ctx | [IN/OUT] TLS Connection Handle |
| int32_t HITLS_GetRecordSizeLimit | ( | HITLS_Ctx * | ctx, |
| uint16_t * | recordSize ) |
Obtains the record size limit value of ctx.
| ctx | [OUT] Hitls ctx |
| recordSize | [IN] the currently in ctx configured record size limit value |
| HITLS_NULL_INPUT | |
| HITLS_SUCCESS |
| int32_t HITLS_GetRenegotiationState | ( | const HITLS_Ctx * | ctx, |
| bool * | isRenegotiationState ) |
Obtain the current is whether in the renegotiation state.
| ctx | [IN] TLS Connection Handle. |
| isRenegotiationState | [OUT] Indicates whether the renegotiation is in the renegotiation state. true: in the renegotiation state; false: not in the renegotiation state. |
| HITLS_SUCCESS,if | successful. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_GetRenegotiationSupport | ( | const HITLS_Ctx * | ctx, |
| bool * | isSupportRenegotiation ) |
Obtain whether renegotiation is supported.
| ctx | [IN] hitls Context |
| isSupportRenegotiation | [OUT] Whether to support renegotiation |
| int32_t HITLS_GetResumptionOnRenegoSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Get whether to support session restoration during renegotiation. By default, session restoration is not supported.
| ctx | [IN] TLS connection handle |
| isSupport | [OUT] Indicates whether to support session restoration during renegotiation. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetRwstate | ( | const HITLS_Ctx * | ctx, |
| uint8_t * | rwstate ) |
Obtain the current internal status.
| ctx | [IN] TLS connection Handle. |
| rwstate | [OUT] Current internal status information. |
| HITLS_SUCCESS,if | successful. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_GetSecureRenegotiationSupport | ( | const HITLS_Ctx * | ctx, |
| bool * | isSecureRenegotiation ) |
Obtains whether security renegotiation is supported.
| ctx | [IN] hitls context. |
| isSecureRenegotiation | [OUT] Whether to support security renegotiation |
| int32_t HITLS_GetSessionTicketSupport | ( | const HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Check whether the session ticket is supported.
| ctx | [IN] TLS connection handle. |
| isSupport | [OUT] whether to support session tickets, true: yes; false: no |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_GetSharedGroup | ( | const HITLS_Ctx * | ctx, |
| int32_t | nmatch, | ||
| uint16_t * | groupId ) |
Obtain the supported peer group or the number of supported peer groups of the nth match. nmatch Value range: - 1 or a positive integer This function can be called only after negotiation and can be called only by the server. If nmatch is a positive integer, check the intersection of groups on the client and server, and return the nmatch group in the intersection by groupId. If the value of nmatch is - 1, the number of intersection groups on the client and server is returned based on groupId.
| ctx | [IN] TLS connection handle. |
| nmatch | [IN] Sequence number of the group to be obtained, -1 Return the number of supported peer groups. |
| groupId | [OUT] Returned result. |
| int32_t HITLS_GetSharedSigAlgs | ( | const HITLS_Ctx * | ctx, |
| int32_t | idx, | ||
| uint16_t * | signatureScheme, | ||
| int32_t * | keyType, | ||
| int32_t * | paraId ) |
Get shared signature algorithms (negotiated)
This function returns the list of signature algorithms supported by both client and server. The algorithms are sorted according to the configured priority policy:
| ctx | [IN] TLS connection handle |
| idx | [IN] Index of algorithm to query (starting from 0)
|
| signatureScheme | [OUT] IANA-defined signature scheme value (uint16_t), can be NULL |
| keyType | [OUT] Certificate key type (HITLS_CERT_KeyType), can be NULL |
| paraId | [OUT] Key parameter ID (CRYPT_PKEY_ParaId), can be NULL |
| > | 0 Total number of shared signature algorithms |
| 0 | Failed (no shared algorithms/idx out of range/version not supported/parameter is NULL) |
| int32_t HITLS_GetShutdownState | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | mode ) |
Obtain the shutdown status of the TLS link.
| ctx | [IN] TLS connection handle. |
| mode | [OUT] TLS shutdown status: HITLS_SENT_SHUTDOWN / HITLS_RECEIVED_SHUTDOWN. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| const char * HITLS_GetStateString | ( | uint32_t | state | ) |
Obtain the handshake status character string.
| state | [IN] Handshake status |
| HITLS_CIPHER_List * HITLS_GetSupportedCiphers | ( | const HITLS_Ctx * | ctx | ) |
Obtain the supported cipher suites list for HITLS_Ctx.
| ctx | [IN] TLS connection handle |
Obtain the UIO object from the HiTLS context.
| ctx | [IN] TLS object. |
| void * HITLS_GetUserData | ( | const HITLS_Ctx * | ctx | ) |
Obtain user data from the HiTLS context. This interface is called in the callback registered with the HiTLS.
| ctx | [OUT] TLS connection handle. |
Obtain user data from the HiTLS context. This interface is called in the callback registered with the HiTLS.
| ctx | [OUT] TLS connection handle. |
| userData | [IN] User identifier. |
| HITLS_SUCCESS | succeeded. |
| HITLS_NULL_INPUT | The input parameter TLS object is a null pointer. |
| int32_t HITLS_GetVerifyNoneSupport | ( | HITLS_Ctx * | ctx, |
| bool * | isSupport ) |
Query if support is available for not performing dual-end verification.
| ctx | [IN] TLS Connection Handle. |
| isSupport | [OUT] if support is available for not performing dual-end verification. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_GetVersionSupport | ( | const HITLS_Ctx * | ctx, |
| uint32_t * | version ) |
Obtain the supported version number.
| ctx | [IN] TLS connection handle. |
| version | [OUT] Supported version number. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_IsAead | ( | const HITLS_Ctx * | ctx, |
| bool * | isAead ) |
Obtain whether to use the AEAD algorithm.
| ctx | [IN] TLS object |
| isAead | [OUT] Indicates whether to use the AEAD algorithm. |
| int32_t HITLS_IsBeforeHandShake | ( | const HITLS_Ctx * | ctx, |
| bool * | isBefore ) |
Check whether the handshake has not been performed.
| ctx | [IN] TLS connection handle |
| isBefore | [OUT] Indicates whether the handshake has not been performed. |
| int32_t HITLS_IsClient | ( | const HITLS_Ctx * | ctx, |
| bool * | isClient ) |
Check whether the current end is client.
| ctx | [IN] TLS connection handle |
| isClient | [OUT] Client or not. |
| int32_t HITLS_IsDtls | ( | const HITLS_Ctx * | ctx, |
| bool * | isDtls ) |
Check whether DTLS is used.
| ctx | [IN] TLS object |
| isDtls | [OUT] Indicates whether to use DTLS. |
| int32_t HITLS_IsHandShakeDone | ( | const HITLS_Ctx * | ctx, |
| uint8_t * | isDone ) |
Obtain the information about whether the handshake is complete.
| ctx | [OUT] TLS connection handle |
| isDone | [IN] Indicates whether the handshake is complete. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_IsHandShaking | ( | const HITLS_Ctx * | ctx, |
| bool * | isHandShaking ) |
Check whether a handshake is being performed.
| ctx | [IN] TLS connection handle |
| isHandShaking | [OUT] Indicates whether the handshake is in progress. |
| int32_t HITLS_IsServer | ( | const HITLS_Ctx * | ctx, |
| bool * | isServer ) |
Indicates whether the HiTLS object functions as the server.
| ctx | [OUT] TLS connection handle |
| isServer | [IN] Indicates whether to function as the server. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_KeyUpdate | ( | HITLS_Ctx * | ctx, |
| uint32_t | updateType ) |
Set the keyupdate type of the current context and send the keyupdate message.
| ctx | [IN] TLS connection handle |
| updateType | [IN] keyupdate type |
| int32_t HITLS_Listen | ( | HITLS_Ctx * | ctx, |
| BSL_SAL_SockAddr | clientAddr ) |
The server statelessly listens for new incoming DTLS connections.
If a ClientHello is received that does not contain a cookie, then server respond with a Hello Verify Request for a new ClientHello that does contain a cookie. If a ClientHello is received with a cookie that is verified, then the function returns in order to enable the handshake to be completed for HITLS_Accept.
| ctx | [IN/OUT] TLS connection handle. |
| clientAddr | [IN/OUT] BSL_SOCKADDR_STORAGE pointed to by peer that sent the ClientHello. |
| HITLS_SUCCESS,the | handshake is successful. |
| For | other error codes, see hitls_error.h. |
| HITLS_Ctx * HITLS_New | ( | HITLS_Config * | config | ) |
Create a TLS object and deep copy the HITLS_Config to the HITLS_Ctx.
This is the main TLS structure, which starts to establish a secure link through the client or server on the basis that the link has been established at the network layer.
| config | [IN] Config context |
Create a TLS object and deep copy the HITLS_Config to the HITLS_Ctx.
| config | [IN] config Context |
| int32_t HITLS_Peek | ( | HITLS_Ctx * | ctx, |
| uint8_t * | data, | ||
| uint32_t | bufSize, | ||
| uint32_t * | readLen ) |
read application data from a TLS/SSL connection
| ctx | [IN] TLS context |
| data | [OUT] data buffer |
| bufSize | [IN] data buffer size |
| readLen | [OUT] store the number of bytes actually read in *readLen |
| HITLS_SUCCESS | |
| HITLS_REC_NORMAL_RECV_BUF_EMPTY,read | buffer is empty, more bytes can be read. |
| HITLS_REC_NORMAL_IO_BUSY,IO | budy, waiting for next calling to read more. |
| Refer | to hitls_error.h for more |
| int32_t HITLS_Read | ( | HITLS_Ctx * | ctx, |
| uint8_t * | data, | ||
| uint32_t | bufSize, | ||
| uint32_t * | readLen ) |
Read application data
| ctx | [IN] TLS context |
| data | [OUT] Read data |
| bufSize | [IN] Size of the buffer |
| readLen | [OUT] Read length |
| HITLS_SUCCESS,if | successful |
| HITLS_REC_NORMAL_RECV_BUF_EMPTY,record | The receiving buffer is NULL and can be read again. |
| HITLS_REC_NORMAL_IO_BUSY,the | network I/O is busy and needs to wait for the next sending You can continue to read the I/O. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_ReadHasPending | ( | const HITLS_Ctx * | ctx, |
| bool * | isPending ) |
Check the HiTLS object in the read cache. (including processed and unprocessed data, excluding the network layer) Whether there is data
| ctx | [IN] TLS connection handle |
| isPending | [OUT] Whether there is data. The options are as follows: 1: yes; 0: no. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_Renegotiate | ( | HITLS_Ctx * | ctx | ) |
Perform renegotiation.
| ctx | [IN] TLS Connection Handle |
| HITLS_SUCCESS,if | successful. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_SetCheckKeyUsage | ( | HITLS_Ctx * | ctx, |
| bool | isCheck ) |
Disables the verification of keyusage in the certificate. This function is enabled by default.
| ctx | [OUT] config context |
| isCheck | [IN] Sets whether to check key usage. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetCipherServerPreference | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
The algorithm suite can be preferentially selected from the algorithm list supported by the server.
| ctx | [IN] TLS Connection Handle. |
| isSupport | [IN] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetCipherSuites | ( | HITLS_Ctx * | ctx, |
| const uint16_t * | cipherSuites, | ||
| uint32_t | cipherSuitesSize ) |
Set the supported cipher suites. The sequence of the cipher suites affects the priority of the selected cipher suites. The cipher suites with the highest priority are selected first.
| ctx | [OUT] TLS connection handle. |
| cipherSuites | [IN] Key suite array, corresponding to the HITLS_CipherSuite enumerated value. |
| cipherSuitesSize | [IN] Key suite array length. |
| int32_t HITLS_SetClientOnceVerifySupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether the client certificate can be requested only once.
| ctx | [OUT] TLS connection handle |
| support | [IN] true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetClientRenegotiateSupport | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
Set whether to allow a renegotiate request from the client
| ctx | [IN/OUT] TLS connection handle. |
| isSupport | [IN] Support or Not,true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_SetClientVerifySupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether to verify the client certificate.
| ctx | [OUT] TLS connection handle |
| support | [IN] Indicates whether to verify the client certificate, the options are as follows: true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetDhAutoSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Sets whether to support the function of automatically selecting DH parameters. If the value is true, the DH parameter is automatically selected based on the length of the certificate private key. If the value is false, the DH parameter needs to be set.
| ctx | [IN/OUT] hitls context. |
| support | [IN] Whether to support. The options are as follows: true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_SetDtlsCookieExangeSupport | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
Sets whether to perform cookie exchange in the dtls.
| ctx | [IN] TLS connection handle. |
| isSupport | [IN] Indicates whether to perform cookie exchange |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetDtlsTimerCb | ( | HITLS_Ctx * | ctx, |
| HITLS_DtlsTimerCb | cb ) |
Set the DTLS timeout interval callback.
| ctx | [IN] TLS connection handle. |
| cb | [IN] DTLS obtaining timeout interval callback. |
| int32_t HITLS_SetEcGroups | ( | HITLS_Ctx * | ctx, |
| uint16_t * | lst, | ||
| uint32_t | groupSize ) |
Set the group supported by the hitls object.
| ctx | [OUT] hitls context |
| lst | [IN] group list |
| groupSize | [IN] List length |
| int32_t HITLS_SetEcPointFormats | ( | HITLS_Ctx * | ctx, |
| const uint8_t * | pointFormats, | ||
| uint32_t | pointFormatsSize ) |
Set the EC point format of the hitls.
| ctx | [OUT] hitls context. |
| pointFormats | [IN] ec point format, corresponding to the HITLS_ECPointFormat enumerated value. |
| pointFormatsSize | [IN] Length of the ec point format |
| int32_t HITLS_SetEmptyRecordsNum | ( | HITLS_Ctx * | ctx, |
| uint32_t | emptyNum ) |
set the max empty records number can be received
| ctx | [IN/OUT] TLS connection handle. |
| emptyNum | [IN] Indicates the max number of empty records can be received |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetEncryptThenMac | ( | HITLS_Ctx * | ctx, |
| bool | encryptThenMacType ) |
Setting the Encrypt-Then-Mac mode.
| ctx | [IN] TLS connection handle. |
| encryptThenMacType | [IN] Current Encrypt-Then-Mac mode. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetEndPoint | ( | HITLS_Ctx * | ctx, |
| bool | isClient ) |
Set the initial status of the connection.
| ctx | [IN] TLS connection handle. |
| isClient | [IN] Set the current client or server. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetErrorCode | ( | HITLS_Ctx * | ctx, |
| int32_t | errorCode ) |
Record the error value of the HiTLS link.
| ctx | [OUT] TLS connection handle |
| errorCode | [IN] Error value |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetExtendedMasterSecretMode | ( | HITLS_Ctx * | ctx, |
| int32_t | mode ) |
Set extended master secret mode.
| ctx | [IN] TLS connection handle |
| mode | [IN] EMS mode. See HITLS_EMS_MODE_*. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,if | ctx is NULL. |
| int32_t HITLS_SetExtendedMasterSecretSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Sets whether to forcibly support extended master keys.
| ctx | [IN] TLS connection handle |
| support | [IN] Indicates whether to forcibly support extended master keys. The options are as follows: True: yes; False: no. The default value is true. |
| HITLS_SUCCESS. | |
| HITLS_NULL_INPUT,ctx | is NULL. |
| int32_t HITLS_SetFlightTransmitSwitch | ( | HITLS_Ctx * | ctx, |
| bool | isEnable ) |
Sets whether to send handshake messages by flight distance.
| ctx | [IN/OUT] TLS connection handle. |
| isEnable | [IN] Indicates whether to enable handshake information sending by flight distance. The value 0 indicates disable, other values indicate enable. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetGroupList | ( | HITLS_Ctx * | ctx, |
| const char * | groups, | ||
| uint32_t | groupNamesLen ) |
Set the group supported during key exchange, the group supported by HiTLS can be queried in HITLS_NamedGroup.
| ctx | [OUT] HiTLS context |
| groups | [IN] Key exchange group. Separate with colons, for example, "HITLS_EC_GROUP_SECP256R1: HITLS_EC_GROUP_SECP384R1" |
| groupNamesLen | [IN] Key exchange group string length |
| int32_t HITLS_SetKeepPeerCertificate | ( | HITLS_Ctx * | ctx, |
| bool | isKeepPeerCert ) |
Set whether to save the peer certificate.
| ctx | [IN] TLS connection handle. |
| isKeepPeerCert | [IN] Set whether to save the peer certificate. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetLegacyRenegotiateSupport | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
Set whether to abort handshake when server doesn't support SecRenegotiation
| ctx | [IN/OUT] TLS connection handle. |
| isSupport | [IN] Support or Not,true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_SetLinkMtu | ( | HITLS_Ctx * | ctx, |
| uint16_t | linkMtu ) |
Set the MTU of Data Link layer.
| ctx | [IN] TLS connection handle |
| linkMtu | [IN] MTU of Data Link layer. |
| HITLS_SUCCESS,set | the mtu succeeded. |
| HITLS_CONFIG_INVALID_LENGTH,the | mtu is invalid For details about other error codes, see hitls_error.h. |
| int32_t HITLS_SetMaxCertList | ( | HITLS_Ctx * | ctx, |
| uint32_t | maxSize ) |
Sets the maximum size of the certificate chain that can be sent from the peer end.
| ctx | [IN/OUT] TLS connection handle. |
| maxSize | [IN] Sets the maximum size of the certificate chain that can be sent from the peer end. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetMaxProtoVersion | ( | HITLS_Ctx * | ctx, |
| uint16_t | version ) |
Set the maximum protocol version that is supported based on the specified version.
| ctx | [OUT] TLS object |
| version | [IN] The given version |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetMaxSendFragment | ( | HITLS_Ctx * | ctx, |
| uint16_t | maxSendFragment ) |
set the max send fragment to restrict the amount of plaintext bytes in any record
| ctx | [IN/OUT] TLS connection handle. |
| maxSendFragment | [IN] Indicates the max send fragment |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_CONFIG_INVALID_LENGTH,the | maxSendFragment is less than 64 or greater than 16384. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetMiddleBoxCompat | ( | HITLS_Ctx * | ctx, |
| bool | isMiddleBox ) |
Sets whether to support middle box compat mode.
| ctx | [IN] TLS Connection Handle. |
| isMiddleBox | [IN] Support or Not. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetMinProtoVersion | ( | HITLS_Ctx * | ctx, |
| uint16_t | version ) |
Set the minimum protocol version based on the specified version.
| ctx | [OUT] TLS object |
| version | [IN] The given version |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetModeSupport | ( | HITLS_Ctx * | ctx, |
| uint32_t | mode ) |
Set the function to support the specified feature.
| ctx | [OUT] TLS connection handle. |
| mode | [IN] features to be enabled. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null |
| int32_t HITLS_SetMtu | ( | HITLS_Ctx * | ctx, |
| uint16_t | mtu ) |
Set the MTU of a path.
| ctx | [IN] TLS connection handle |
| mtu | [IN] Set the MTU. |
| int32_t HITLS_SetNeedCheckPmsVersion | ( | HITLS_Ctx * | ctx, |
| bool | needCheck ) |
Sets whether to verify the version in the premaster secret.
| ctx | [OUT] TLS Connection Handle. |
| needCheck | [IN] Indicates whether to perform check. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetNoClientCertSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether to support the function without the client certificate, Takes effect only when the client certificate is verified. Client: This setting has no impact Server: When an NULL certificate is received from the client, indicates whether the certificate passes the verification, the verification fails by default.
| ctx | [OUT] TLS connection handle |
| support | [IN] Indicates whether the authentication is successful when there is no client certificate. true: If the certificate sent by the client is NULL, the server still passes the verification. false: If the certificate sent by the client is NULL, the server fails the verification. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetNoQueryMtu | ( | HITLS_Ctx * | ctx, |
| bool | noQueryMtu ) |
Set the option that don't query mtu from the bio.
| ctx | [IN] TLS connection handle |
| noQueryMtu | [IN] whether not to query the mtu from the bio. |
| HITLS_SUCCESS,set | the option succeeded. For details about other error codes, see hitls_error.h. |
| int32_t HITLS_SetPostHandshakeAuthSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether to support post-handshake AUTH.
| ctx | [OUT] TLS connection handle |
| support | [IN] true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetQuietShutdown | ( | HITLS_Ctx * | ctx, |
| int32_t | mode ) |
Set the silent disconnection mode.
| ctx | [IN] TLS connection handle. |
| mode | [IN] Mode type. The value 0 indicates that the quiet disconnection mode is disabled, and the value 1 indicates that the quiet disconnection mode is enabled. |
Read UIO for the HiTLS context.
| ctx | [OUT] TLS connection handle. |
| uio | [IN] UIO object. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetRecInbufferSize | ( | HITLS_Ctx * | ctx, |
| uint32_t | recInbufferSize ) |
Set the rec inbuffer inital size
| ctx | [IN/OUT] TLS connection handle. |
| recInbufferSize | [IN] Indicates the rec inbuffer inital size |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_CONFIG_INVALID_LENGTH,the | recInbufferSize is less than 512 or greater than 18432. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetRecordPaddingCb | ( | HITLS_Ctx * | ctx, |
| HITLS_RecordPaddingCb | callback ) |
Sets the RecordPadding callback.
| ctx | [IN/OUT] TLS Connection Handle |
| callback | [IN] Sets the RecordPadding callback. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetRecordPaddingCbArg | ( | HITLS_Ctx * | ctx, |
| void * | arg ) |
Sets the parameters arg required by the RecordPadding callback function.
| ctx | [IN/OUT] TLS Connection Handle |
| arg | [IN] Related Parameter arg |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
| int32_t HITLS_SetRecordSizeLimit | ( | HITLS_Ctx * | ctx, |
| uint16_t | recordSize ) |
The default record size limit is 0 to unsupport the record size limit extension (RFC 8449). If negotiated, it is used only to limit the size of records sent by the peer in the receive direction. However, the record size sent to the peer is limited by the record size limit value of the peer.
| ctx | [OUT] Hitls config |
| recordSize | [IN] Set the default record size limit value to be negotiated (64 to 16385) |
| HITLS_NULL_INPUT | |
| HITLS_SUCCESS |
| int32_t HITLS_SetRenegotiationSupport | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
Sets whether to support renegotiation.
| ctx | [IN/OUT] TLS connection handle. |
| isSupport | [IN] Support or Not,true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_SetResumptionOnRenegoSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether to support session restoration during renegotiation. By default, session restoration is not supported.
| ctx | [IN] TLS connection handle |
| support | [IN] Whether to support the function. The options are as follows: True: yes; False: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,ctx | is null. |
| int32_t HITLS_SetServerName | ( | HITLS_Ctx * | ctx, |
| uint8_t * | serverName, | ||
| uint32_t | serverNameStrlen ) |
Setting the value of server_name.
| ctx | [IN] TLS connection handle. |
| serverName | [IN] serverName. |
| serverNameStrlen | [IN] serverName length. |
| int32_t HITLS_SetSessionTicketSupport | ( | HITLS_Ctx * | ctx, |
| bool | isSupport ) |
Sets whether to support session tickets.
| ctx | [IN/OUT] TLS connection handle. |
| isSupport | [IN] whether to support session tickets, true: yes; false: no |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| int32_t HITLS_SetShutdownState | ( | HITLS_Ctx * | ctx, |
| uint32_t | mode ) |
Set the shutdown status of the TLS link.
| ctx | [IN] TLS connection handle. |
| mode | [IN] TLS shutdown status: HITLS_SENT_SHUTDOWN / HITLS_RECEIVED_SHUTDOWN. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
| int32_t HITLS_SetSigalgsList | ( | HITLS_Ctx * | ctx, |
| const uint16_t * | signAlgs, | ||
| uint16_t | signAlgsSize ) |
Set the signature algorithm supported by the hitls object.
| ctx | [OUT] hitls context. |
| signAlgs | [IN] List of supported signature algorithms. |
| signAlgsSize | [IN] Length of the signature algorithm list. |
| int32_t HITLS_SetTmpDh | ( | HITLS_Ctx * | ctx, |
| HITLS_CRYPT_Key * | dhPkey ) |
Set the DH parameter specified by the user.
| ctx | [IN/OUT] hitls context. |
| dhPkey | [IN] User-specified DH key. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT | ctx or dhPkey field is NULL |
| int32_t HITLS_SetTmpDhCb | ( | HITLS_Ctx * | ctx, |
| HITLS_DhTmpCb | callback ) |
Set the TmpDh callback function.
| ctx | [IN/OUT] TLS connection handle. |
| callback | [IN] Set the TmpDh callback. |
| HITLS_NULL_INPUT,the | input parameter pointer is NULL. |
| HITLS_SUCCESS,if | successful. |
Set the UIO object for the HiTLS context.
Bind the HiTLS context to the UIO object, through which the TLS object sends data, reads data, and controls the connection status at the network layer. After successfully setting, the number of times the UIO object is referenced increases by 1. BSL_UIO_Free is called to release the association between the HiTLS and UIO when HITLS_Free is called.
| ctx | [OUT] TLS connection handle. |
| uio | [IN] UIO object. |
| HITLS_SUCCESS,if | successful. |
| For | other error codes, see hitls_error.h. |
Set the UIO object for the HiTLS context.
| ctx | [OUT] TLS connection handle. |
| uio | [IN] UIO object |
| int32_t HITLS_SetUserData | ( | HITLS_Ctx * | ctx, |
| void * | userData ) |
Save the user data in the HiTLS context, which can be obtained from the callback registered with the HiTLS.
| ctx | [OUT] TLS connection handle. |
| userData | [IN] Pointer to the user data. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,the | TLS object pointer of the input parameter is null. |
Save the user data in the HiTLS context, which can be obtained from the callback registered with the HiTLS.
| ctx | [OUT] TLS connection handle. |
| userData | [IN] User identifier. |
| HITLS_SUCCESS | succeeded. |
| HITLS_NULL_INPUT | The input parameter TLS object is a null pointer. |
| int32_t HITLS_SetVerifyNoneSupport | ( | HITLS_Ctx * | ctx, |
| bool | support ) |
Set whether to support do not proceed dual-ended verification.
| ctx | [OUT] TLS connection handle |
| support | [IN] true: yes; false: no. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetVersion | ( | HITLS_Ctx * | ctx, |
| uint32_t | minVersion, | ||
| uint32_t | maxVersion ) |
Set the supported version number range.
| ctx | [OUT] TLS connection handle |
| minVersion | [IN] Minimum version number supported. |
| maxVersion | [IN] Maximum version number supported. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetVersionForbid | ( | HITLS_Ctx * | ctx, |
| uint32_t | noVersion ) |
Set the version number to be disabled.
| ctx | [OUT] TLS connection handle |
| noVersion | [IN] Disabled version number. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_SetVersionSupport | ( | HITLS_Ctx * | ctx, |
| uint32_t | version ) |
Set the supported version number.
| ctx | [OUT] TLS connection handle |
| version | [IN] Supported version number. |
| HITLS_SUCCESS,if | successful. |
| HITLS_NULL_INPUT,config | is null. |
| int32_t HITLS_VerifyClientPostHandshake | ( | HITLS_Ctx * | ctx | ) |
This interface is valid only on the server. When the post-handshake command is configured, the client identity is verified through this interface.
| ctx | [IN] TLS Connection Handle |
| HITLS_INVALID_INPUT,invalid | input parameter. |
| HITLS_SUCCESS,if | successful. |
| For | details about other error codes, see hitls_error.h. |
| int32_t HITLS_Write | ( | HITLS_Ctx * | ctx, |
| const uint8_t * | data, | ||
| uint32_t | dataLen, | ||
| uint32_t * | writeLen ) |
Write data.
: Encrypts and packs data with the specified length dataLen into a single record and sends the record.
| ctx | [IN] TLS context |
| data | [IN] Data to be written |
| dataLen | [IN] Length to be written |
| writeLen | [OUT] Length of Successful Writes |
| HITLS_SUCCESS | is sent successfully. |
| HITLS_REC_NORMAL_RECV_BUF_EMPTY,record | If the receiving buffer is NULL, the message can be sent again. |
| HITLS_REC_NORMAL_IO_BUSY,The | network I/O is busy and needs to wait for the next sending. You can continue sending the I/O. |
| For | other error codes, see hitls_error.h. |